SafeNet DPoD Cloud HSM
The SafeNet DPoD (Data Protection on Demand) service provides HSM on Demand which is one of HSM’s on Demand Services. This section introduces how to generate key on Cloud HSM and use it. Please see the SafeNet Official Guide if you need details or other information. Click " " icon on your site on SafeNet DPoD Service, to avail the guide.
" icon on your site on SafeNet DPoD Service, to avail the guide.
Before proceeding, we should understand the 3 types of users in the DPoD role hierarchy which are as follows:
No | Type | Responsibility | Note |
|---|---|---|---|
1 | Service Provider Administrators | Managing and distributing additional DPoD tenants. | On this document, there is no description about this user. Please see the SafeNet Official Guide. |
2 | Tenant Administrators | Managing an enterprise tenant and distributing cryptographic resources in the form of services to application owners. | The user can create, subscribe group and Application Owner, and configure services. |
3 | Application Owners | Managing cryptographic services, and consuming cryptographic resources in an enterprise tenant. |
Install LunaClient
Add a Subscriber Group as Tenant Administrator
Sign in to DPoD site using your Tenant Administrator credential.
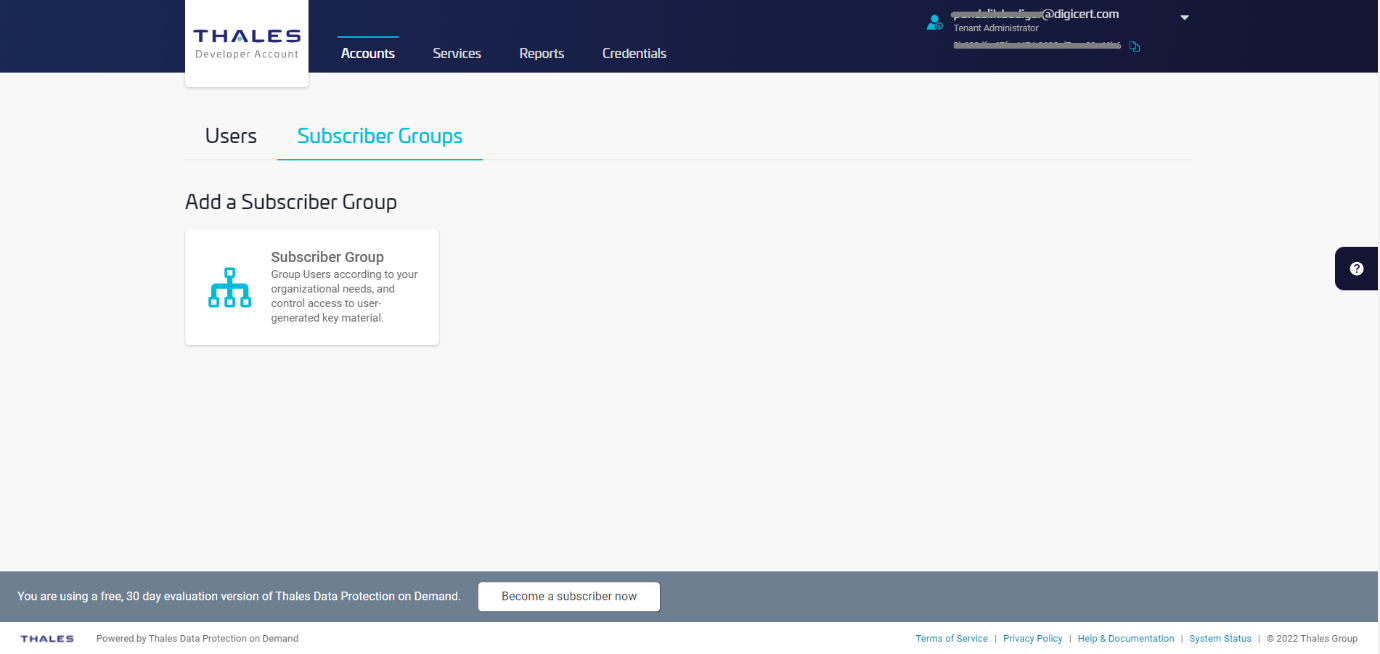
Select Subscriber Groups followed by Subscriber Group tile.
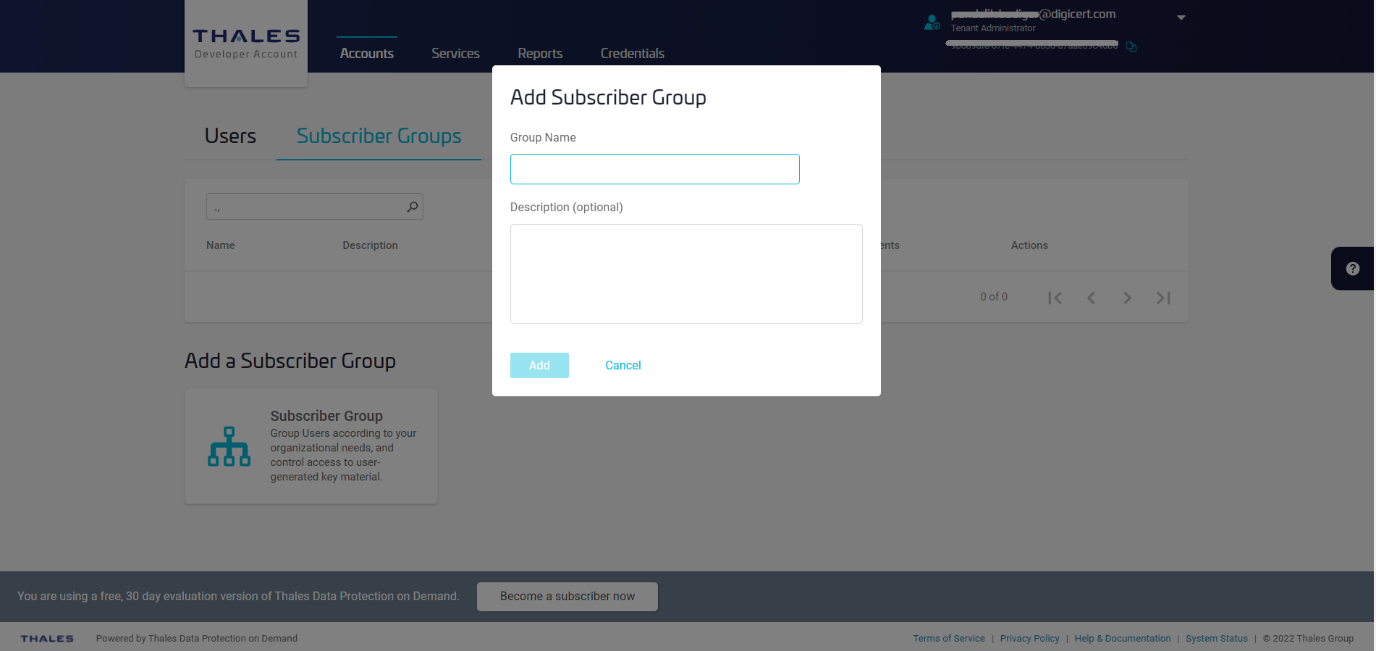
Enter Group Name and Description and then click Add.
In this document, Group Name is DPPC-QA but you can use any other value.
The designated group has been created.
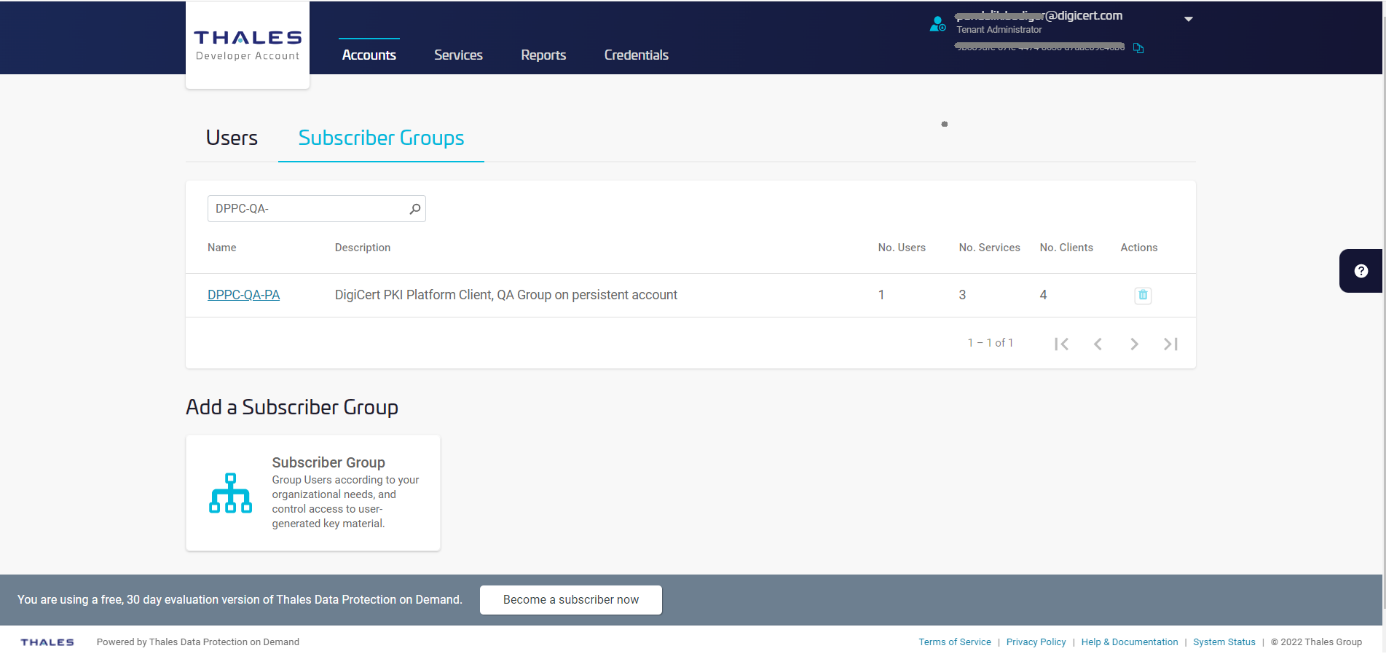
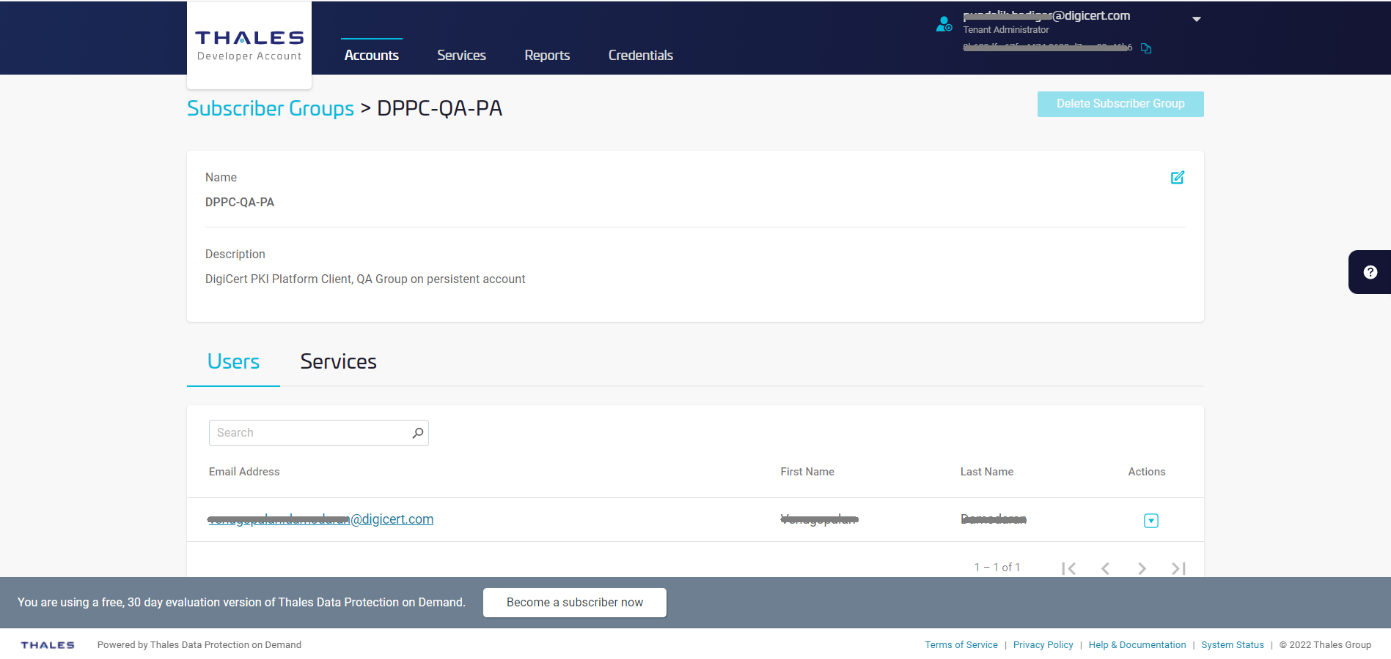
Click on the link of group which has been created to view the Group details.
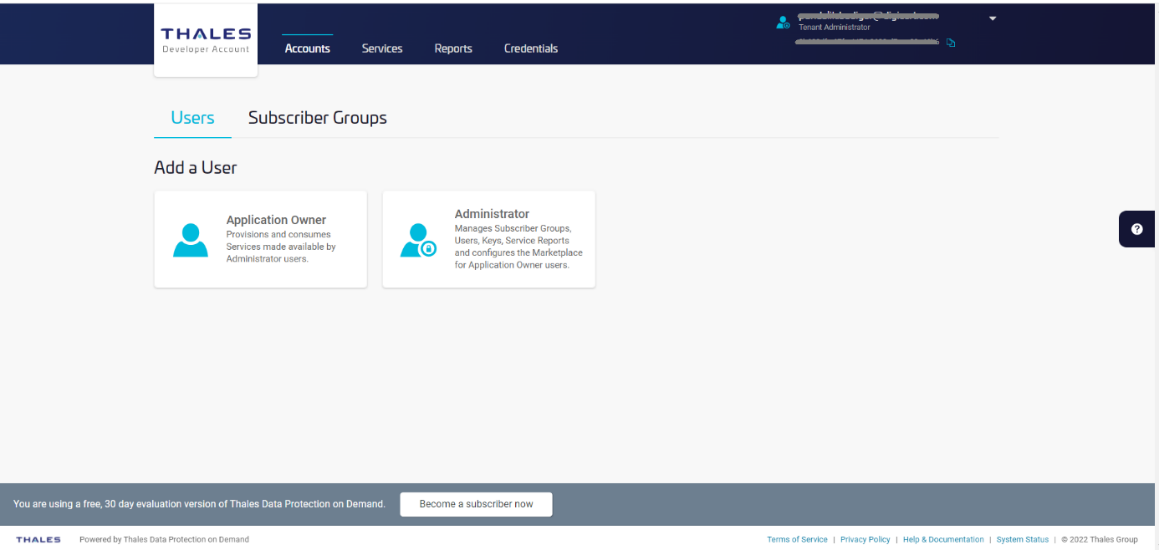
Add an Application Owner as Tenant Administrator
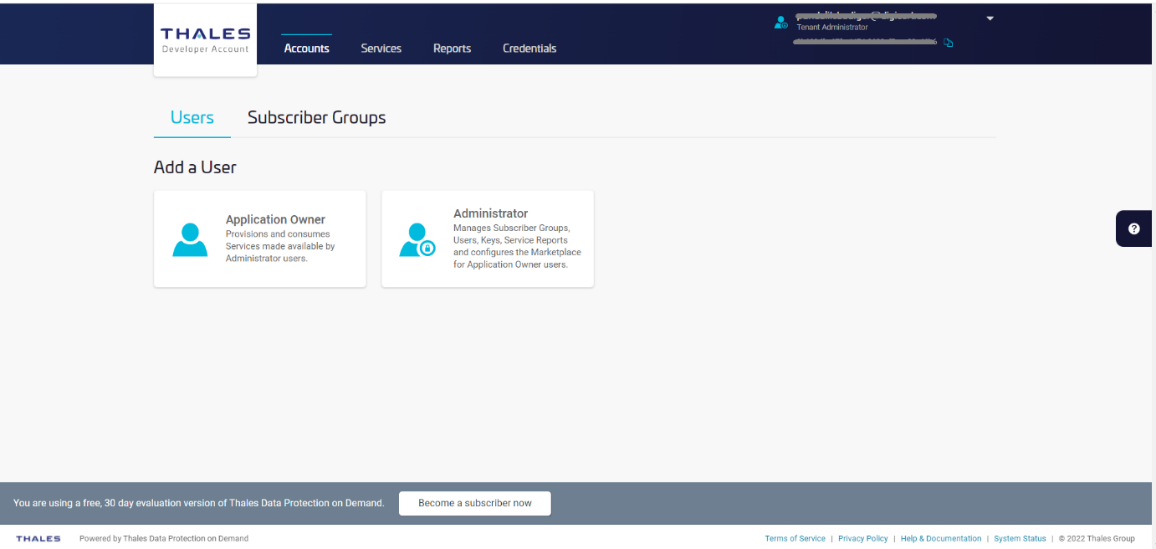
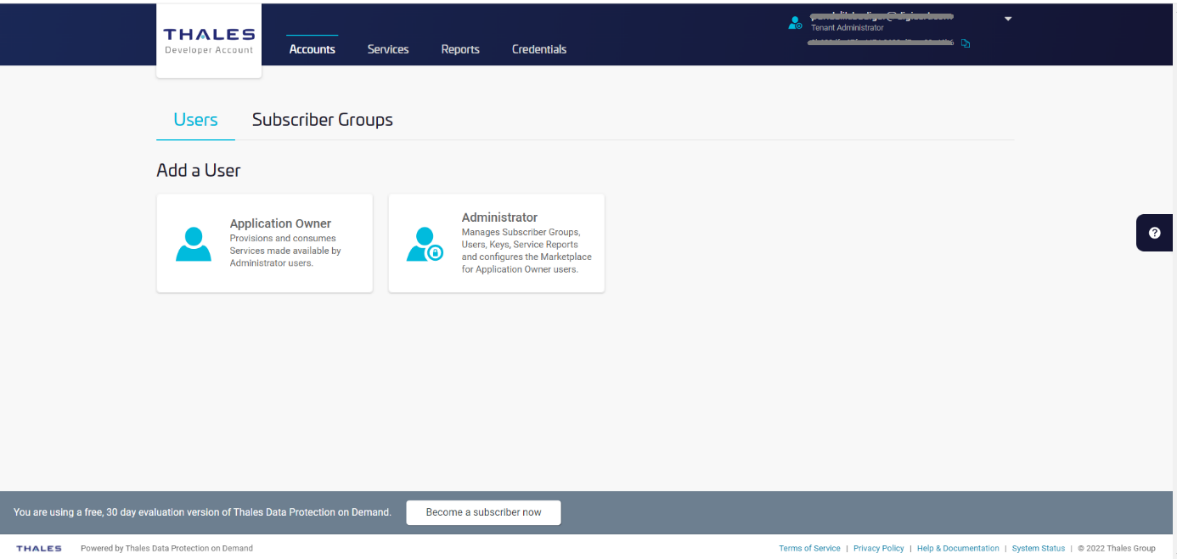
Sign in to DPoD site using your Tenant Administrator credential. Select Accounts tab and Select Users and Select Application Owner, under Add a User.
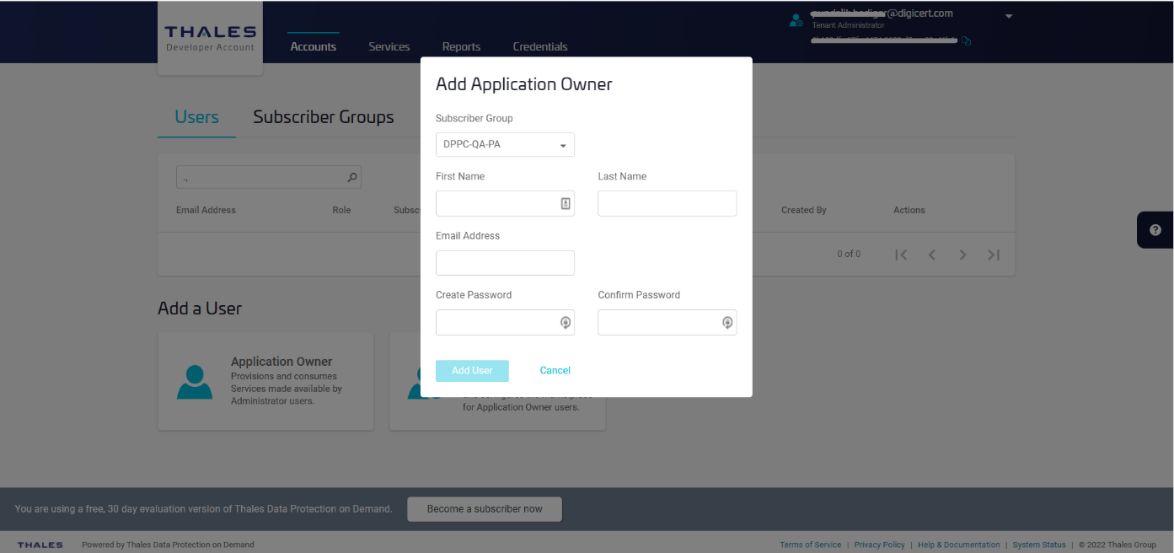
Fill out the form with the user details and then click Add User.
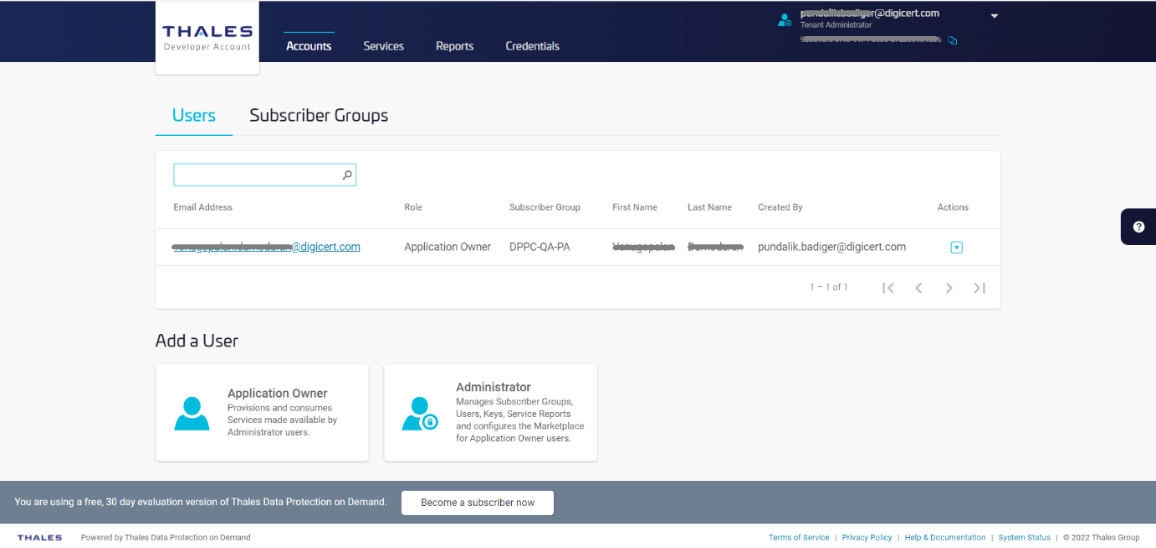
The user is created.
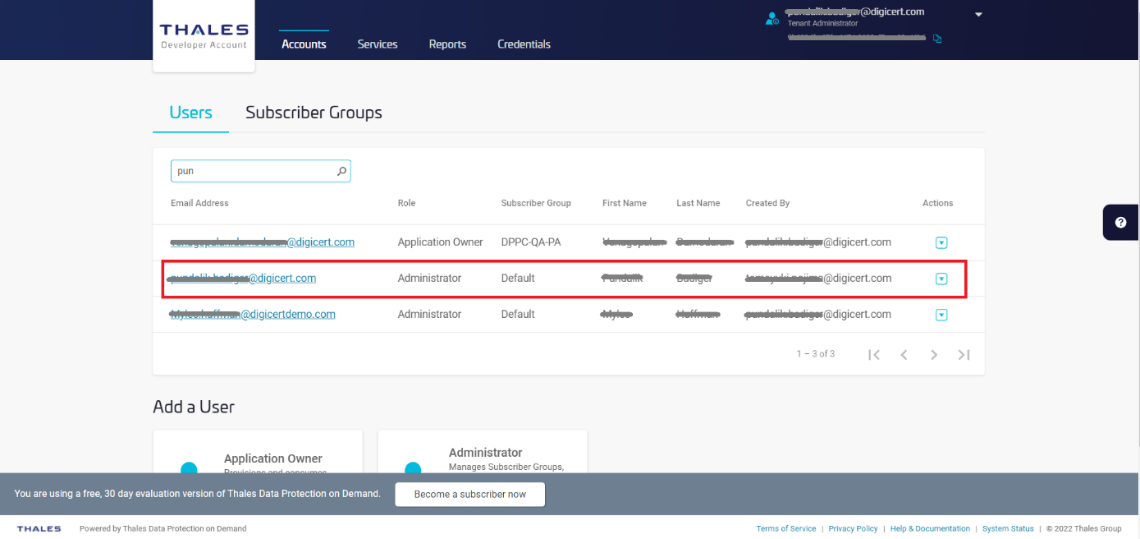
Add Administrator as Tenant Administrator
Sign in DPoD site and Select Accounts tab and select Users and select Administrator, under Add a User.
Fill out the form with the Administrator details then click Add User.
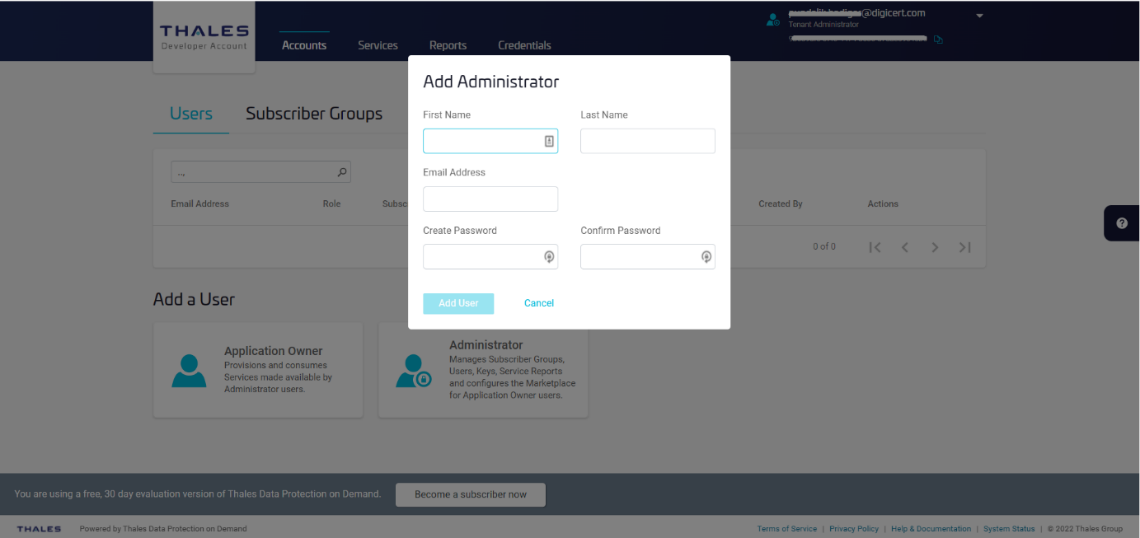
The Administrator is created.
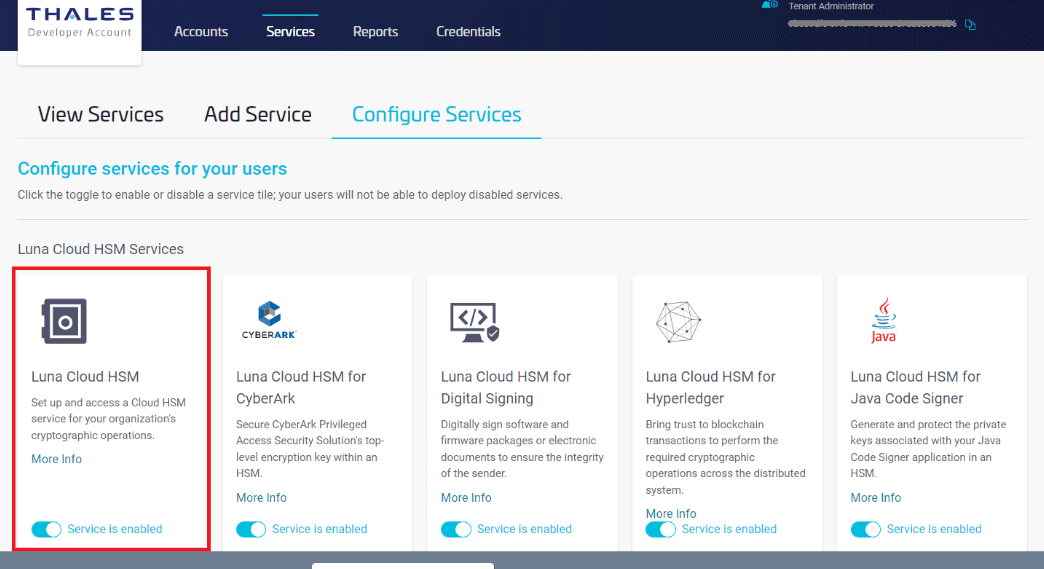
Enable Luna Cloud HSM Services as Tenant Administrator
Select Services tab then click on Configure Services.
Under the Luna Cloud HSM service tile (Set up and access a Cloud HSM service for your organization’s cryptographic operations), click the toggle to enable service.
Add New Services and Service Client as Application Owner
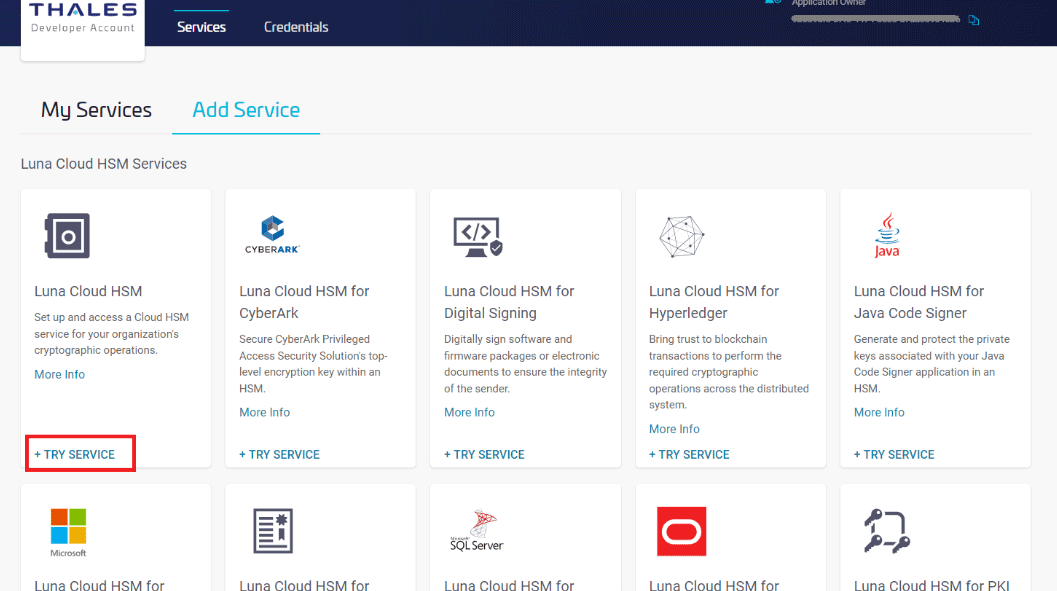
Sign in as an Application Owner and then select Add New Service and click on +TRY SERVICE under the Luna Cloud HSM service tile.
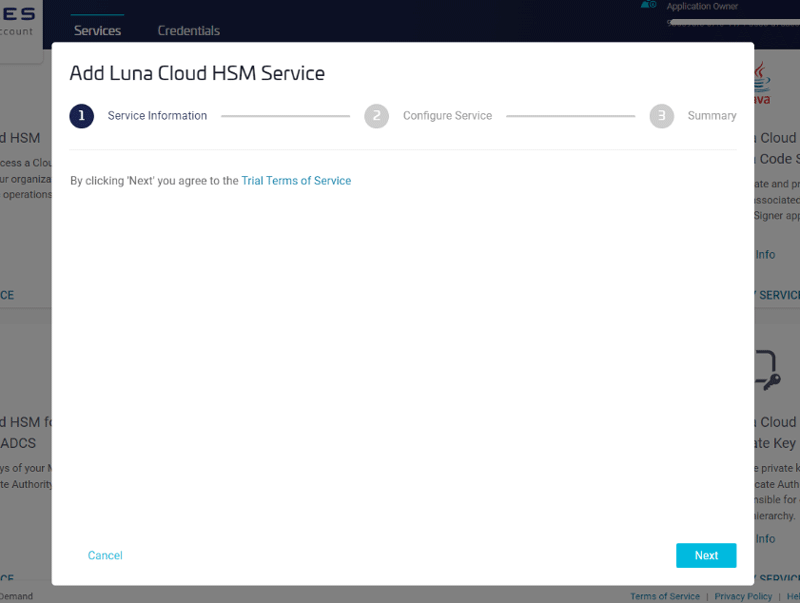
Step 1: Service Information.
Click Next (By clicking 'Next' you agree to the Trial Terms of Service)
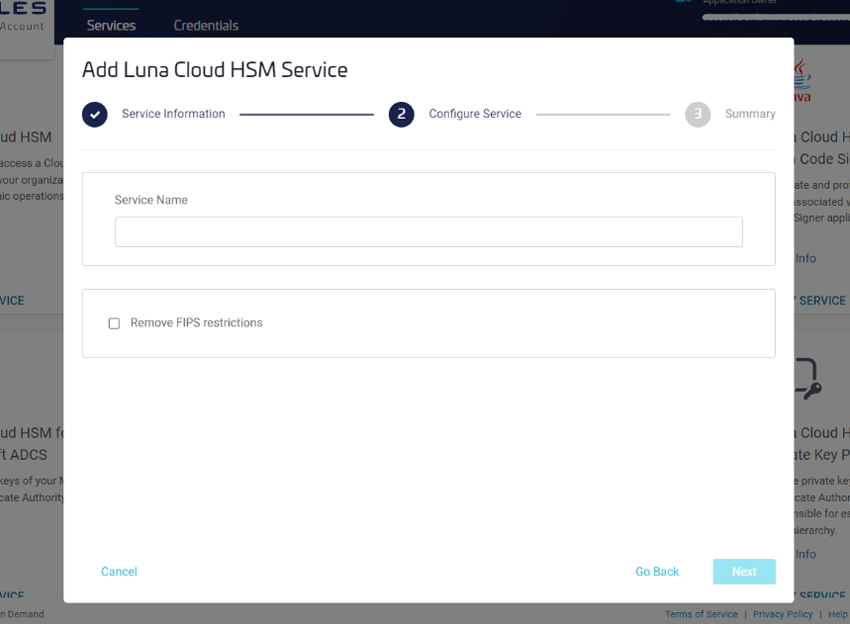
Step 2: Configure Service.
Enter Service Name and check if you wish to opt for Remove FIPS restrictions, and then click Next.
Step 3: Summary
Confirm your Service Name and click Finish.
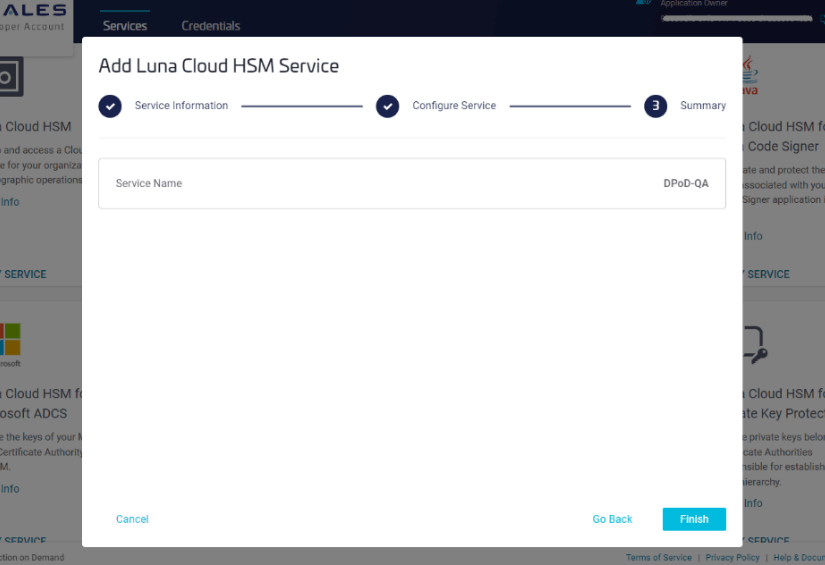
It takes several seconds for processing.
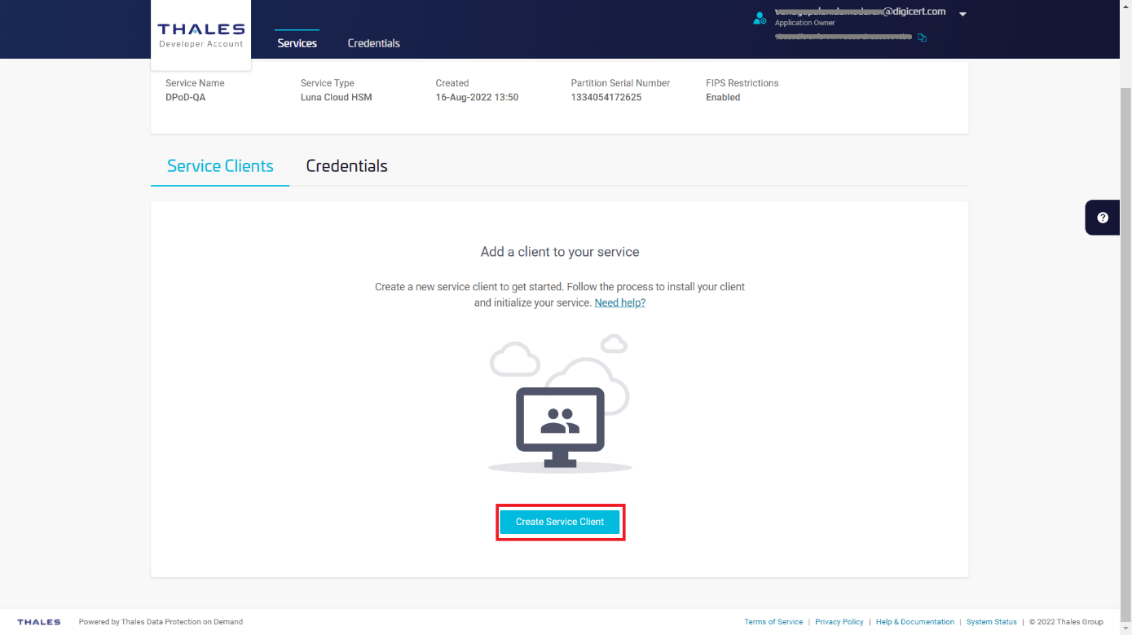
Click Create Service Client.
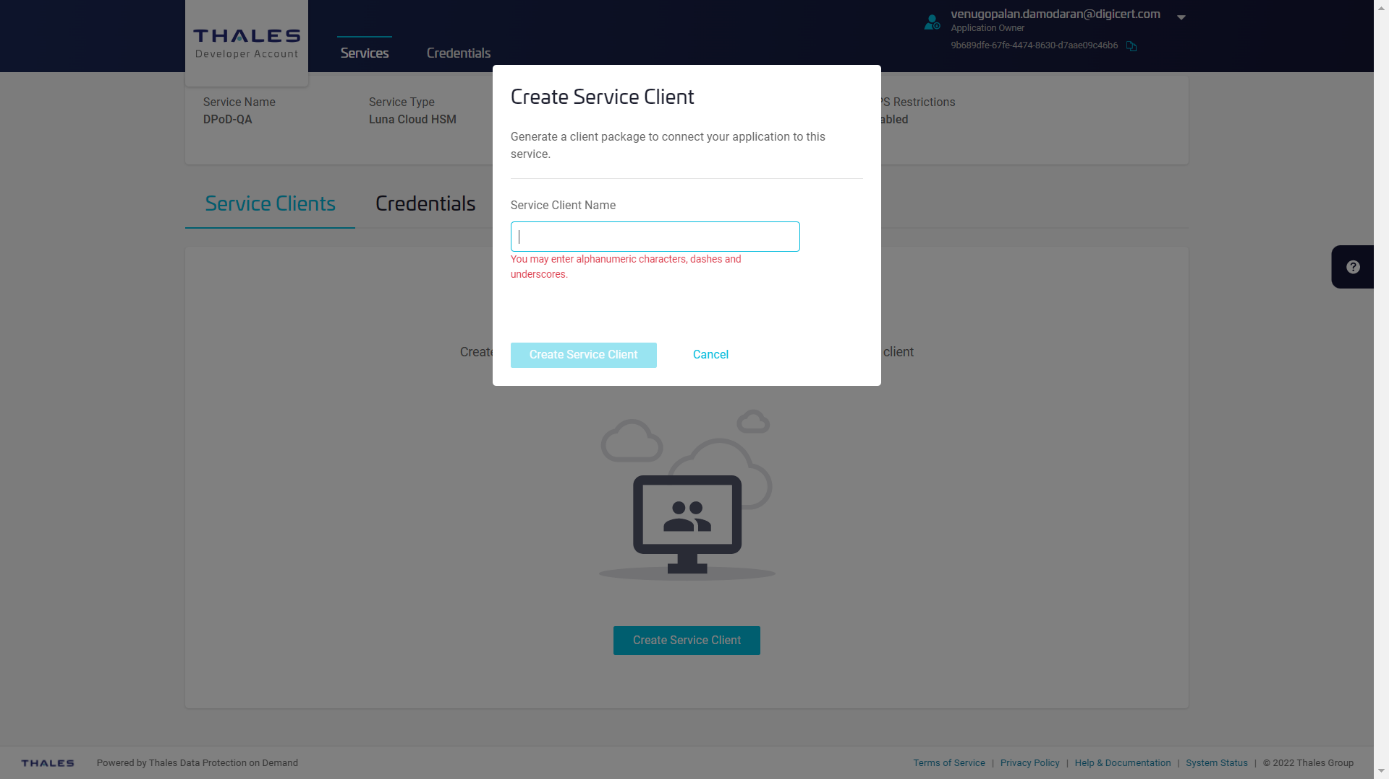
Enter Service Client Name and then click Create Service Client.
It takes several seconds to process.
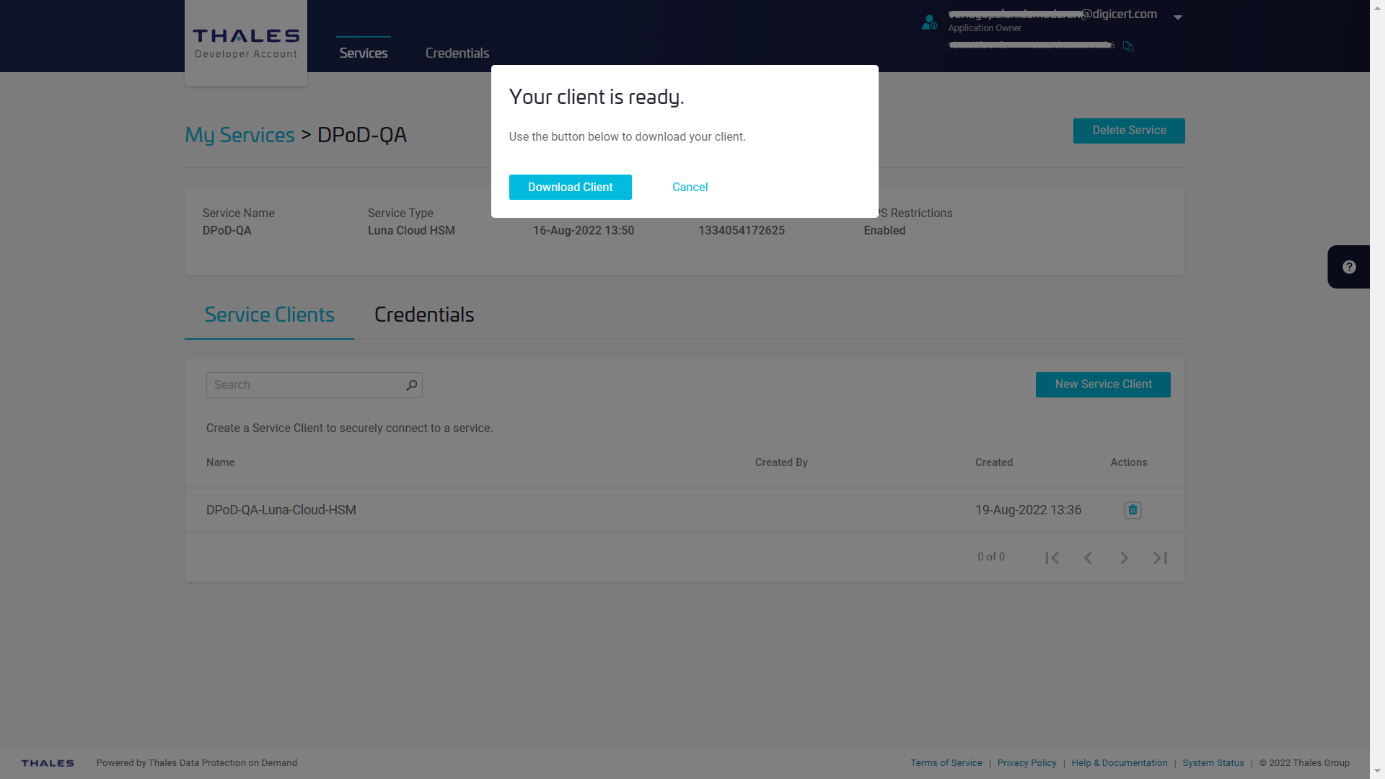
Click Download Client to download the service client software onto your workstation.
The name of the archive file will be setup-<Service Client Name>.zip. All the tools are included into the file.
Install Service Client for Windows
The Windows service client installation uses a .zip file to deliver the HSM on Demand (HSMoD) service client materials required for configuring your system's connection to the HSMoD service. The service client .zip includes a pre-configured crystoki-template.ini file along with a client archive file containing a set of library and binary files. Complete the following procedures to access your HSMoD service from a Windows operating system.
Extract the downloaded archive file.
Using the Windows GUI or an unzip tool, unzip the file. The extracted files are as follows:
26-09-2022 05:48 1,327 Chrystoki.conf 26-09-2022 05:48 1,129 crystoki-template.ini 26-09-2022 05:48 30,289,920 cvclient-min.tar 26-09-2022 05:48 8,483,712 cvclient-min.zip 26-09-2022 05:48 187,032 EULA.zip 26-09-2022 05:48 8,176 partition-ca-certificate.pem 26-09-2022 05:48 1,387 partition-certificate.pem 26-09-2022 05:48 5,660 server-certificate.pem
Extract the cvclient-min-zip file.
Using the Windows GUI or an unzip tool, unzip the file at the same folder. The extracted files are as follows:
26-07-2022 21:13 <DIR> cert 26-07-2022 21:13 <DIR> csp 26-07-2022 21:13 <DIR> ksp 26-07-2022 21:13 <DIR> plugins 26-07-2022 21:13 <DIR> WindowsEventProvider 26-09-2022 05:48 1,327 Chrystoki.conf 26-07-2022 21:13 510,184 ckdemo.exe 26-07-2022 21:13 1,844,968 cmu.exe 26-07-2022 21:13 4,267,752 cryptoki.dll 26-09-2022 05:48 1,129 crystoki-template.ini 26-09-2022 05:48 30,289,920 cvclient-min.tar 26-09-2022 05:48 8,483,712 cvclient-min.zip 26-09-2022 05:48 187,032 EULA.zip 26-07-2022 21:13 212,200 LunaAPI.dll 26-07-2022 21:13 3,701,992 lunacm.exe 26-07-2022 21:13 697,965 LunaProvider.jar 26-07-2022 21:13 568,040 multitoken.exe 26-07-2022 21:13 7,145 openssl.cnf 26-09-2022 05:48 8,176 partition-ca-certificate.pem 26-09-2022 05:48 1,387 partition-certificate.pem 26-07-2022 21:13 194,280 SafeNetKSP.dll 26-09-2022 05:48 5,660 server-certificate.pem 26-07-2022 21:13 490 setenv.cmd 26-07-2022 21:13 32,155 setenv.ps1 26-07-2022 21:13 2,166,504 vtl.exe
Nota
Extract the cvclient-min.zip within the directory you created in the previous step. Do not extract to a new cvclient-min.zip directory. This location is required for the setenv command in the next step.
Please remove crystoki.ini if it exists before moving to next.
Set the environment variable.
Open Command Prompt as Administrator, then move to the directory where the cvclient-min file has been extracted and run the following command:
> setenv.cmd Generated C:\Users\Test\CloudHSM\setup-DPPC-CloudHSM\crystoki.ini
The crystoki.ini is as follows:
[Chrystoki2] LibNT=C:\Users\Test\CloudHSM\setup-DPPC-CloudHSM\cryptoki.dll LibNT32=C:\Users\Test\CloudHSM\setup-DPPC-CloudHSM\cryptoki.dll [CardReader] RemoteCommand=1 LunaG5Slots=0 [Luna] DefaultTimeOut=500000 PEDTimeout1=100000 PEDTimeout2=200000 PEDTimeout3=20000 KeypairGenTimeOut=2700000 CloningCommandTimeOut=300000 CommandTimeoutPedSet=720000 [Presentation] ShowEmptySlots=no [Misc] PE1746Enabled=1 ToolsDir=C:\Program Files\SafeNet\LunaClient\ PluginModuleDir=C:\Users\Test\CloudHSM\setup-DPPC-CloudHSM\plugins WindowsEventProvider=C:\Users\Test\CloudHSM\setup-DPPCCloudHSM\WindowsEventProvider\LunaClientEventProvider.dll [XTC] Enabled=1 TimeoutSec=600 [LunaSA Client] SSLConfigFile=C:\Users\Test\CloudHSM\setup-DPPC-CloudHSM\openssl.cnf ReceiveTimeout=20000 TCPKeepAlive=1 NetClient=1 ServerCAFile=C:\Users\Test\CloudHSM\setup-DPPCCloudHSM\cert\server\CAFile.pem ClientCertFile=C:\Users\Test\CloudHSM\setup-DPPCCloudHSM\\cert\client\ClientNameCert.pem ClientPrivKeyFile=C:\Users\Test\CloudHSM\setup-DPPCCloudHSM\cert\client\ClientNameKey.pem [REST] AuthTokenConfigURI=https://lab-digicert.uaa.system.snakefly.dpsas.io/.wellknown/openid-configuration AuthTokenClientId=4dd589be-1d9d-43b1-9cf0-faee5f5006c5 AuthTokenClientSecret=XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX RestClient=1 ClientTimeoutSec=120 ClientPoolSize=32 ClientEofRetryCount=15 ClientConnectRetryCount=900 ClientConnectIntervalMs=1000 ServerPort=443 ServerName=na.hsm.dpondemand.io
Nota
At that time, ChrystokiConfigurationPath will set on this directory.
The crystoki.ini file will be generated.
Start LunaCM.
Start LunaCM. From the directory where you unzipped the cvclient-min.zip file, execute lunacm.exe. If the command executes with no errors, your connection is working correctly.
>lunacm.exe lunacm.exe (64-bit) v10.5.0-470. Copyright (c) 2022 SafeNet. All rights reserved. Available HSMs: Slot Id -> 3 Label -> DPoD-QA-Luna-Cloud-HSM Serial Number -> 1334054172625 Model -> Cryptovisor7 Firmware Version -> 7.3.0 CV Firmware Version -> 1.5.0 Plugin Version -> Cloud 2.2.0-740 Configuration -> Luna User Partition With SO (PW) Signing With Cloning Mode Slot Description -> Net Token Slot FM HW Status -> FM Not Supported Current Slot Id: 3
Nota
If you use proxy server, you need to set environment variable of https_proxy as follows;
> set https_proxy=http://<proxy-server>/<port>
Configure LunaClient
Initialize the partition and users
Set the active slot.
Select the uninitialized application partition.
lunacm:> slot set -slot 3 Current Slot Id: 3 (Luna User Slot 7.3.0 (PW) Signing With Cloning Mode) Command Result : No Error
Nota
You can verify the slot number by executing slot list in lunacm.
Initialize the application partition.
Create a partition for the Security Officer (SO), set the initial password, domain name for cloning purposes, and respond to the prompts:
lunacm:> partition init -label DPPC-QA You are about to initialize the partition. Are you sure you wish to continue? Type 'proceed' to continue, or 'quit' to quit now -> proceed Enter password for Partition SO: ******** Re-enter password for Partition SO: ******** Option -domain was not specified. It is required. Enter the domain name: ****** Re-enter the domain name: ****** Command Result : No Error
Nota
Label: DPPC-QA and Domain: DEVJP
Log in as Partition SO.
Run the following command to login into the partition as the Security Officer (SO) - you can use the shortcut po.
lunacm:> role login -name po enter password: ******** Command Result : No Error
Initialize the Crypto Officer role and set the initial password.
Run the following command to initialize the Crypto Office (CO) role - you can use the shortcut co:
lunacm:> role init -name co enter new password: ******** re-enter new password: ******** Command Result : No Error
Log out.
The Partition SO can create the Crypto Officer, but only the Crypto Officer can create the Crypto User. You must log out to allow the Crypto Officer to login with the newly-set password.
lunacm:> role logout Command Result : No Error
Nota
Once the Crypto Officer logs in and changes the initial credential set by the Partition SO, applications using the CO's challenge secret/password can perform cryptographic operations in the partition. The Crypto Officer can create, modify and delete crypto objects within the partition, and use existing crypto objects (sign/verify). You can also create a limited-capability role called Crypto User that can use the objects created by the Crypto Officer but cannot modify them. The separation of roles is important in some security regimes and operational situations, and where you might be required to satisfy audit criteria for industry or government oversight.
Log in as the Crypto Officer.
lunacm:> role login -name co enter password: ******** Command Result : No Error
Nota
The password for the Crypto Officer role is valid for the initial login only. You must change the initial password using the command role changepw during the initial login session, or a subsequent login. Failing to change the password will result in a CKR\_PIN\_EXPIRED error when you perform role-dependent actions.
If you have not already done so, change the initial password set by the Partition SO.
lunacm:> role changepw -name co enter existing password: ******** enter new password: ******** re-enter new password: ******** Command Result : No Error
Create the Crypto User.
lunacm:> role init -name cu enter new password: ******** re-enter new password: ******** Command Result : No Error
The Crypto User can now log in with the credentials provided by the Crypto Officer and change the initial password. The Crypto User can now use applications to perform cryptographic operations using keys and objects created in the partition by the Crypto Officer.
Nota
The password for the Crypto User role is valid for the initial login only. The CU must change the initial password using the command role changepw during the initial login session, or a subsequent login. Failing to change the password will result in a CKR\_PIN\_EXPIRED error when they perform role-dependent actions.
Login as Crypt User.
lunacm:> role logout Command Result : No Error lunacm:> role login -name cu enter password: ******** Command Result : No Error
Change the password for Crypto User.
lunacm:> role changepw -name cu enter existing password: ******** enter new password: ******** re-enter new password: ******** Command Result : No Error
Nota
The initial PIN should be changed.
Configure High Availability (HA)
Nota
The feature does not support on DPoP Service but there are redundant systems with several LunaPCI on Thales backend. Therefore, it is not required to configure any HA group.
Configure CSP
For SafeNet CSP, the utility register.exe takes care of the registry. To configure CSP, open command prompt as Administrator and run the following commands.
Register CSP Library
C:\Users\Test\CloudHSM\setup-DPPC-CloudHSM\csp>register.exe /library register.exe (64-bit) v10.5.0-470. Copyright (c) 2022 SafeNet. All rights reserved. Success registering SOFTWARE\Microsoft\Cryptography\Defaults\Provider\Luna enhanced RSA and AES provider for Microsoft Windows. Success registering SOFTWARE\Microsoft\Cryptography\Defaults\Provider\Luna Cryptographic Services for Microsoft Windows. Success registering SOFTWARE\Microsoft\Cryptography\Defaults\Provider\Luna SChannel Cryptographic Services for Microsoft Windows.
Register the partition
C:\Users\Test\CloudHSM\setup-DPPC-CloudHSM\csp>register.exe register.exe (64-bit) v10.5.0-470. Copyright (c) 2022 SafeNet. All rights reserved. *************************************************************************** * * * Safenet LunaCSP, Partition Registration * * * * Protect the HSM's challenge for the selected partitions. * * * * NOTE: * * This is a WEAK protection of the challenge. * * After you have configured all applications that will use * * the LunaCSP and ran them once, you MUST run: * * register /partition /strongprotect * * to strongly protect the registered challenges. * * * *************************************************************************** This is a destructive procedure and will overwrite any previous registrations. Do you wish to continue?: [y/n]y Do you want to register the partition named ''?[y/n]: y Enter Crypto-Officer challenge for partition '' :************ Success registering the encrypted challenge for partition ":3". Registered 1 partition(s) for use by the LunaCSP.
Configure KSP
To configure KSP(CNG), run KspConfig.exe. Follow instructions for the use of the graphical KspConfig.exe as described in KSP for CNG in the SDK Reference Guide. The following window appears:
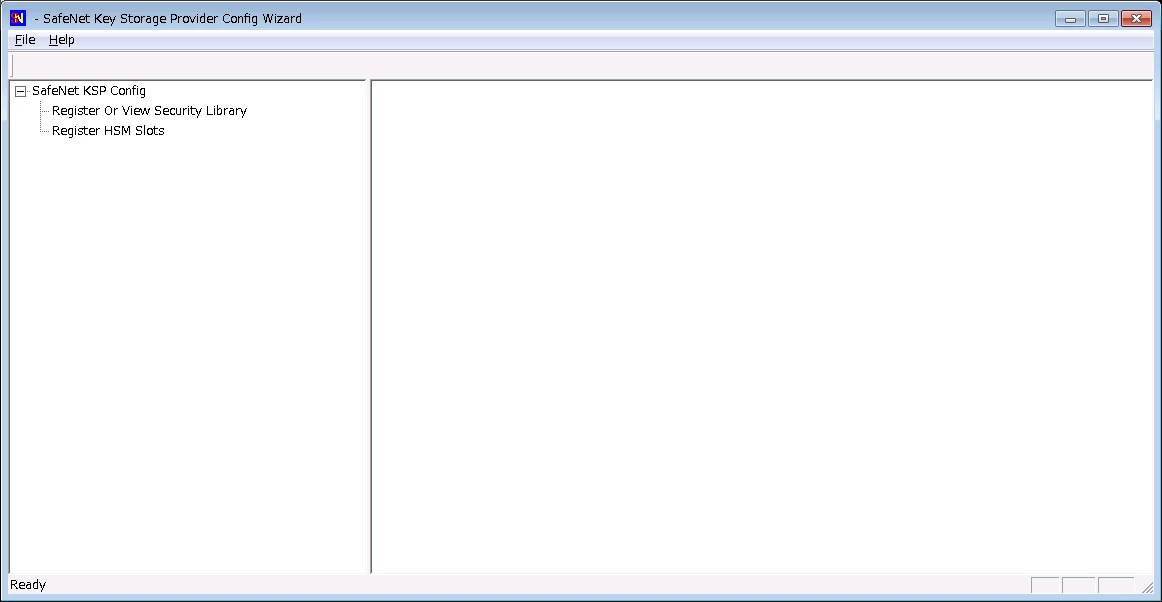
Double-click Register Or View Security Library, then you can select the value <extracted-directory>\cryptoki.dll.
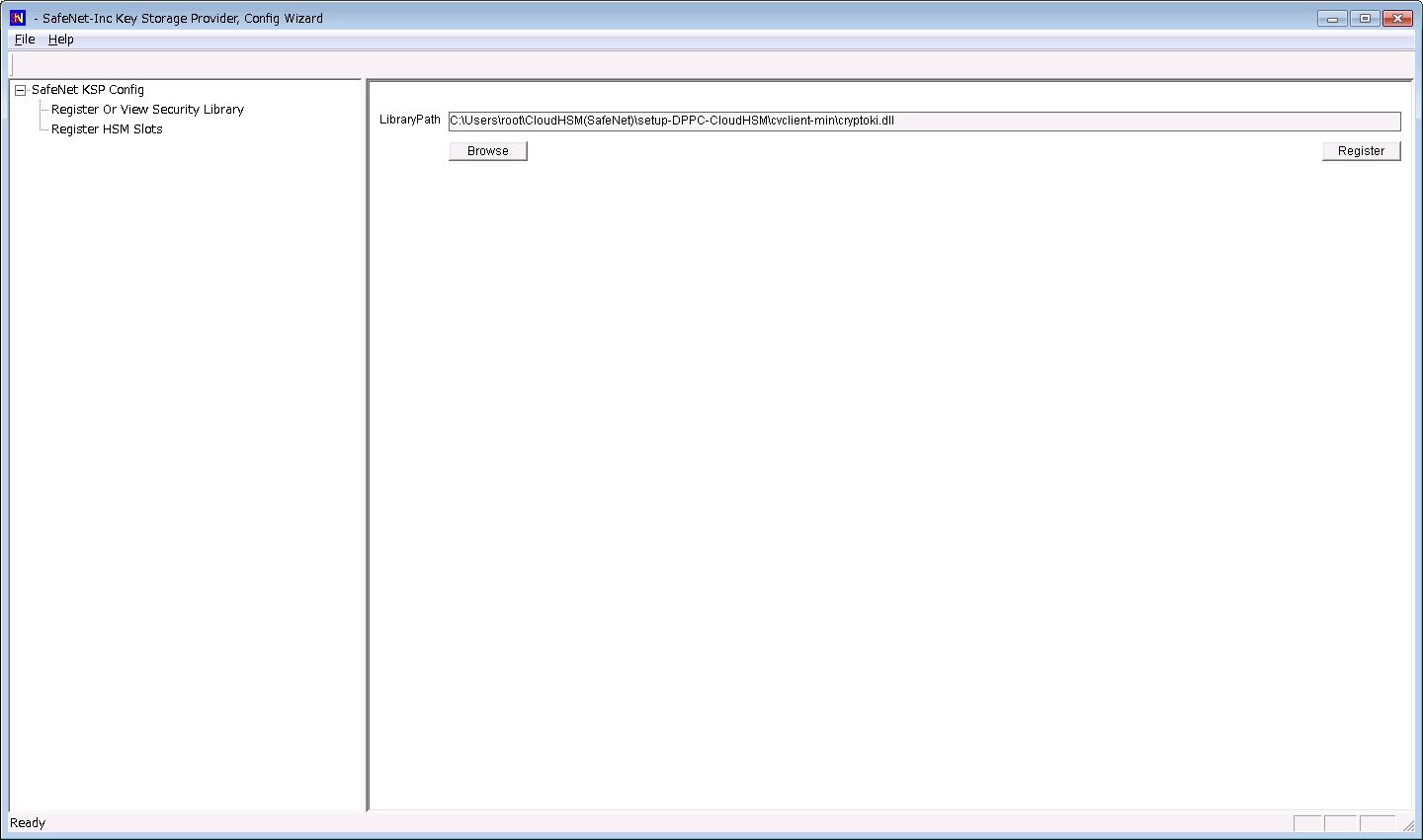
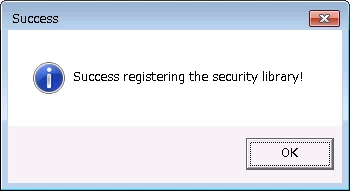
Click on Register button, and you can see the below message.
Double-click Register HSM Slots for Administrator/<Domain Name>
Select Administrator
Select <Domain Name>
Select the Group Name (DPPC-QA) for Available Slots
Enter Slot Password
Click Register Slot.
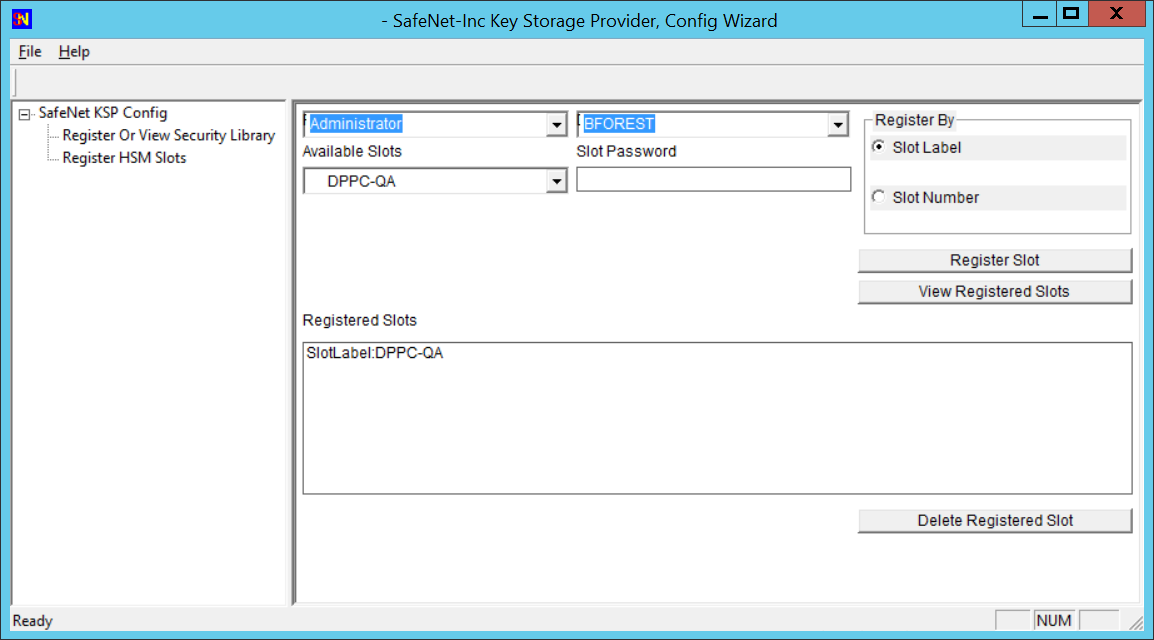
Nota
When you click Register Slot, there is no change, but this step is necessary.
When registering the Luna KSP (with the Luna KSPConfig utility), use the following user and domain combinations:
The user and domain performing these procedures.
The user and domain running the web application and using the private key.
The local user and NT Authority domain user.
The LocalSystem and NTAuthority of the system.
Nota
If you implement the Autoenrollment server, you must also install and register the Luna CSP. Refer to the Luna product documentation for details.
Generate CSR and Install Certificate
Create the information file for CSR.
To generate CSR through certreq.exe via CSP, the ProviderName must be Luna Cryptographic Services for Microsoft Windows. A sample inf file is shown below:
[NewRequest] KeyUsageProperty = "NCRYPT_ALLOW_ALL_USAGES" RequestType = PKCS10 ProviderName = "Luna Cryptographic Services for Microsoft Windows" ProviderType = 1 Subject = "CN=Registration Authority" KeyContainer = "CSPRA20221001" MachineKeySet = TRUE HashAlgorithm = SHA256 KeyAlgorithm = RSA KeyLength = 2048
Generate CSR through HSM.
Copy the SafeNetKSP.dll and LunaCSP.dll to C:\Windows\System32, then open the command prompt as Administrator and run the following command.
> certreq -new <inf-file> <csr-file>
The CSR file will be generated as follows:
-----BEGIN NEW CERTIFICATE REQUEST----- MIIDjzCCAncCAQAwITEfMB0GA1UEAwwWUmVnaXN0cmF0aW9uIEF1dGhvcml0eTCC .... C610uaqncn6FvLu5pygZYFEVtOanCXNQRRUWiDGWKjHF+10GMh+V5YUur55T4W80 0uwK -----END NEW CERTIFICATE REQUEST-----
Get an RA Certificate.
Install RA certificate.
Get a client authentication certificate
This section describes steps to get a client authentication certificate using the Generic User Certificate template, CSR Enrollment Method, and Enrollment Code as Authentication Method. But you can get a client authentication certificate using any of the combinations below:
Template | Enrollment Method | Authentication Method |
|---|---|---|
Generic User Certificate | CSR | Manual Approval |
Generic User Certificate | REST API | Enrollment Code or 3rd Party app |
Generic Device Certificate | CSR | Manual Approval or Enrollment Code |
Generic Device Certificate | REST API | Enrollment Code or 3rd Party app |
Create profile
Sign into DigiCert ONE and navigate to Trust Lifecycle Manager.
Select Manage Profiles from the left navigation menu, then Profiles.
Select Add profile.
Select the Generic User Certificate template.
Note: The appropriate license for the seat type of the template selected must be purchased and available in your account, otherwise that template’s link will be disabled.
Under the General information section, enter the profile Nickname and choose the Business Unit and Issuing CA.
From the Enrollment method dropdown, select CSR.
From the Authentication method dropdown, select Enrollment Code.
Select Next.
Under Certificate fields, select the validity period unit (Years, Months, or Days) and enter the value in the textbox.
Note: You cannot issue an end entity certificate with a validity period longer than the remaining validity of the issuing CA. The issuing CA expiration date is shown as a reference in this section.
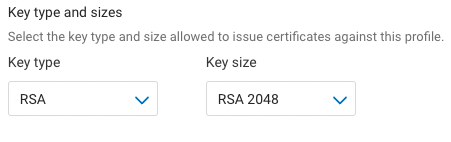
Select the Algorithm from the available algorithms in the dropdown list. Available algorithms are based on the issuing CA selected for the profile.
Select the Key type and attribute from the dropdown lists.
Select the checkbox to Allow duplicate certificates if multiple certificates are to be issued for the same seat ID.
Under Renewal options, select the Renewal window from the dropdown list. The default (recommended) value is 30 days.
Select Subject DN and SAN fields from the dropdown list. Select the Common name field, then select Add fields.
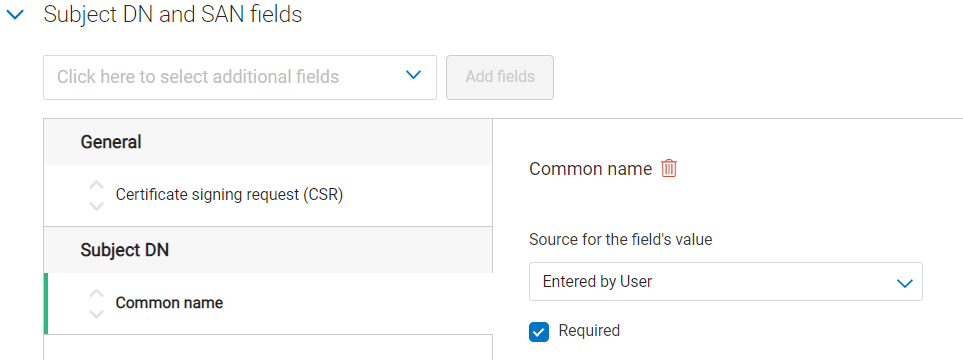
For each selected field, from the Source for the field’s value dropdown, select Entered by user.
Select Next.
Specify the Key usage (KU) extension criticality and values. Note: the KU options shown differ depending on the certificate template being used.
Specify the Extended key usage (EKU) extension criticality and values. Note: Client Authentication is the minimum required EKU value.
Select Next.
Under Certificate delivery format, select PKCS#7 PEM and Include CA chain with Root CA as the certificate delivery format to use and chain certificates to include when certificates are issued.
Under Email configuration & notifications, specify the template to be used for certificate revocation notification emails.
Under Administrative contact, specify whether to include default or custom administrative contact details in certificate notification emails. Note: including internal support contact details for end users is optional, but recommended.
Under Seat ID Mapping, select the certificate field to be used as the seat ID. This uniquely identifies each enrollment entity, for licensing purposes.
Select Create. Your newly created certificate profile is now displayed in the certificate profiles list.
Add User/Device Seat
Select Manage Seats from the left navigation menu, then Add user seat.
Enter a Seat name.
Enter a Seat ID.
Enter an Email (optional).
Enter Phone details (optional).
Select a Business Unit.
Select Create user seat.
Select Enroll Now.
Select the profile created in the Create Profile section from the Choose A Profile dropdown.
Select Enroll.
Copy the Enrollment Code that is required to get the certificate.
Access the link provided in the email.
Enter the Enrollment Code copied in step 11.
Enter the Certificate signing request (CSR) that was generated in the Generate CSR section.
Enter the Common name.
Select Update.
Download the certificate.
Upload client authentication certificate
Navigate to Account Manager.
Select Access from the left navigation menu, then Service User.
Select the Service user for which you are uploading the client authentication certificate.
Select Upload Client authentication certificate under the Authentication certificates section.
Enter a Nickname.
Export the client authentication certificate downloaded under the Add User/Device Seat Section (step 17) in DER or PEM format. Select Click or drag file to upload and choose the certificate.
Select Upload client authentication certificate.
Install RA certificate
Open the command prompt (on the folder where the PKCS#7 file is stored) and run the following command:
> certreq -accept <issued-cert>
Before running the command above, the trusted root certificate must first be installed. If not, the following error will be displayed:
Certificate Request Processor: A certificate chain could not be built to a trusted root authority. 0x800b010a (-2146762486 CERT_E_CHAINING)