Configure single sign-on with OIDC
Follow these steps to enable single sign-on (SSO) with OpenID Connect (OIDC) in your DigiCert ONE account. If another sign in method is also enabled, you can select which method to use.
Prerequisites
Before configuring OIDC in DigiCert ONE:
Have administrator access to your company's identity provider (IDP) service, such as Micosoft Entra ID, PingOne, and Okta.
Register DigiCert ONE as an OIDC application with your identity provider (IDP).
Configure your IDP to send a
preferred_usernameclaim in the ID token.
Tip
To learn how to register applications for OIDC and configure claims, refer to the documentation for your IDP.
Configure OIDC in DigiCert ONE
In the Managers () menu, select Account.
In the Account menu, go to Accounts.
On the Accounts page, in the Name column, select the account you want enable OIDC authentication for.
On the Account details page, under Sign in settings for all-account-access users, find Single sign-on with OIDC. Select Edit.
On the Update OpenID Connect integration page, select the option to Enable OIDC authentication.
From the Update OpenID Connect integration page, copy the following values, and provide them to your IDP wherever you configure the OIDC integration with DigiCert ONE.
Redirect / callback URL: When users sign in to an OIDC-enabled account, your OIDC service generates an authentication response and token ID. The OIDC service sends this authentication information back to DigiCert ONE using this URL.
Login initiation endpoint: DigiCert-provided URL that users can access to sign in to DigiCert ONE using OIDC-based SSO.
Logout endpoint: Your OIDC provider uses the logout endpoint to sign the user out of any applications they’ve logged into via the provider.
Under Enter this information from your OIDC service, enter the information your IdP provides for each of these values.
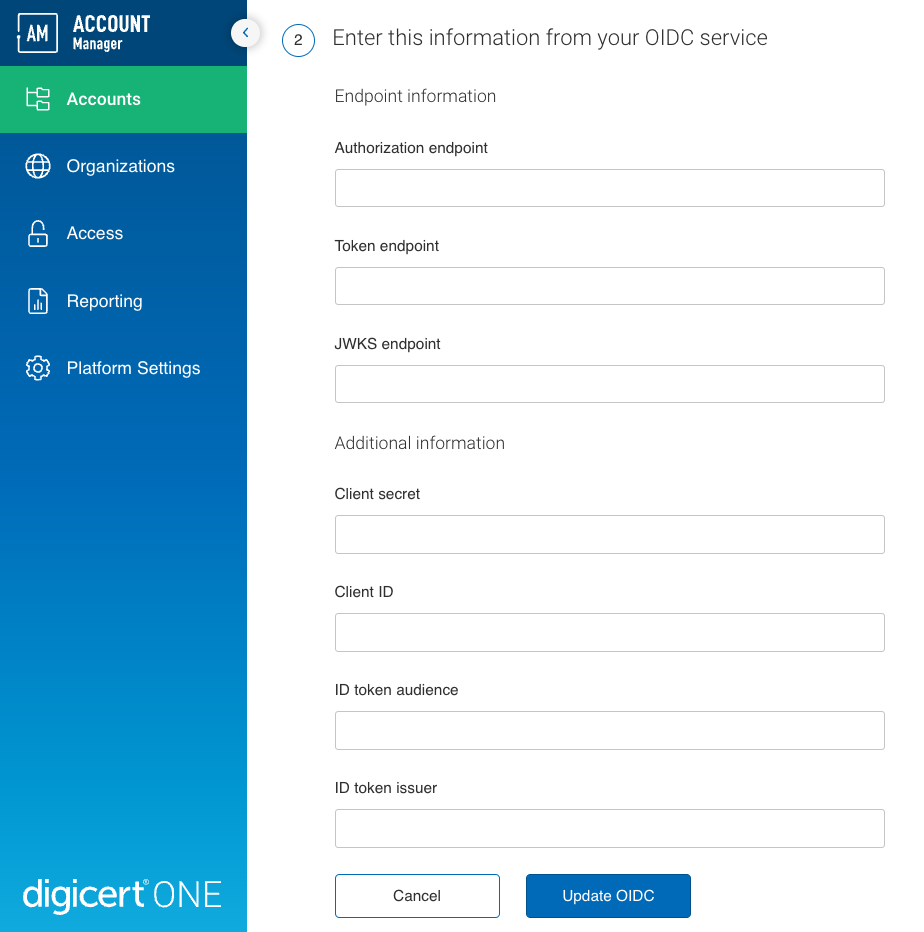
Authorization endpoint: Authorization endpoint for your OIDC service.
Token endpoint: Endpoint on the authorization server that DigiCert ONE can use to request access tokens from your OIDC service.
JWKS endpoint: Endpoint on the authorization server that DigiCert ONE can use to request a JSON Web Key Set (JWKS) with the public keys to verify access token signatures.
Client secret: Password from your IDP that DigiCert ONE can use to authenticate requests to your OIDC service.
Client ID: ID from your IDP that DigiCert ONE can use to identify itself in requests to your OIDC service.
ID token audience: Intended recipient of ID tokens your OIDC service generates. Must match the ID token audience configured in your IDP.
ID token issuer: Name (URL) of the ID token issuer for your OIDC service. Must match the ID token issuer configured in your IDP.
Select Update OIDC to save your settings in DigiCert ONE.
Troubleshooting
To configure SSO with OIDC, you need to create an OIDC application for DigiCert® account in your IdP. During the process of creating this application, you need to provide DigiCert URLs. When the application is created, you need to provide to DigiCert® account with specific values from the OIDC application you created.
Tip
To perform this action, you must be an admin in your IdP.
Select your IdP:
Select your IdP:
Select your IdP:
Select your IdP:
What's next
Finish any remaining steps in your IdP to finalize the connection to DigiCert ONE
DigiCert ONE sends existing users in your account the Single sign-on access to DigiCert email. The email lets them know you enabled SSO for their account.
Two-factor authentication (2FA) and SSO with OIDC
When 2FA is enabled, DigiCert skips the one-time password (OTP) prompt if you have already provided an OTP to your IdP.