- DigiCert product docs
- What's new
- Change log
- CertCentral
CertCentral
Change log RSS
Upcoming changes
March 1, 2027
Removing the client authentication EKU from public TLS certificates
Notice
Important update: Google Chrome updated their root program requirements extending the timeline for removing the Client Authentication extended key usage (EKU) from public TLS certificates.
DigiCert will now stop including the Client Authentication EKU in public TLS certificates on March 1, 2027. We originally planned this for May 1, 2026. Read our knowledge base article about removing the Client Authentication EKU from public TLS certificates.
Beginning March 1, 2027, DigiCert will stop issuing public TLS certificates with the Client Authentication extended key usage (EKU). Per Google Chrome’s root program requirements, we’ll issue all public TLS certificates with the Server Authentication EKU.
This change doesn't affect your existing TLS certificates with the Client Authentication EKU issued before March 1, 2027. These existing certificates remain trusted until they expire. However, if you reissue, duplicate, or renew your TLS certificate as of March 1, 2027, we’ll issue it without the Client Authentication EKU.
What should I do to prepare for the Client Authentication EKU removal from public TLS certificates?
Do you also use TLS certificates for client authentication?
We use TLS certificates for securing website (HTTPS).
If using your TLS/SSL certificates solely for securing websites (HTTPS), then no action is required.
However, DigiCert recommends reviewing your TLS certificate process to verify it's used just for securing websites. Disruption could occur if your certificates intended for client authentication don't include the Client Authentication EKU.
We use TLS certificates for Mutual TLS (mTLS), server-to-server authentication, or other authentication use cases.
If your organization requires the Client Authentication EKU in your DigiCert TLS certificates for mTLS or server-to-server authentication, then action is required.
DigiCert has excellent options available for our customers and partners who require the client authentication EKU beyond March 1, 2027.
Possible solutions if you require the Client Authentication EKU in your DigiCert TLS certificates
X9 PKI for TLS certificates
Transition to DigiCert’s X9 PKI for TLS certificates to secure communications involving multiple organizations. Regulated by the ASC X9 standards body, X9 PKI is governed by an independent certificate policy unaffiliated with the browsers. However, it ensures interoperability by using a common root of trust. X9 PKI for TLS certificates can have both client and server authentication EKUs. These certificates meet today's need for control, security, flexibility, and scalability with encryption, identity, and cross-certification capabilities. Learn more about X9 PKI and schedule a consultation.
Private trust
Transition to Private PKI as a service for business needs that are strictly internal. DigiCert can configure and operate a private PKI for your organization, applying our operational expertise and investments in security. Learn more.
Non-browser public trust
Transition to existing DigiCert root hierarchies for business needs that require non-browser ubiquity. You can use these DigiCert root hierarchies to issue TLS certificates that include the clientAuth EKU:
DigiCert Assured ID Root G2 (RSA)
DigiCert Assured ID Root G3 (ECC)
TLS certificates issued from these hierarchies won’t be trusted in Google Chrome or Mozilla Firefox. Contact your account representative to learn if this option is right for you.
Why will DigiCert stop including the client authentication EKU in public TLS certificates?
This change aligns with Google Chrome’s root program requirements to enhance security and promote interoperability. For more information about DigiCert's timeline for phasing out the Client Authentication EKU, read Removing the client authentication EKU from public TLS certificates.
DigiCert stopped including the Client Authentication EKU in public TLS certificates by default
On October 1, 2025, DigiCert stopped including the Client Authentication EKU in public TLS certificates by default. We now issue public TLS certificates with just the Server Authentication EKU. However, you can still include the ClientAuth EKU in your TLS certificates if you need TLS certificates with client authentication. For a limited time, from now until to March 1, 2027, CertCentral includes two new EKU options on the public TLS/SSL certificate request forms. Learn more about these EKU options.
June 6, 2026
Included in this update:
Upcoming scheduled Europe maintenance
DigiCert will perform scheduled maintenance on June 6, 2026, from17:00 - 19:00 CEST (15:00 - 17:00 UTC).
How does scheduled maintenance affect my CertCentral services?
We don’t expect this maintenance to affect CertCentral services. However, some other DigiCert services may be unavailable during the maintenance window.
Other DigiCert services
To learn how maintenance affects other DigiCert services, like the QuoVadis PrimoSign signing service, see the June 6 entry in the DigiCert Europe 2026 maintenance schedule.
What can I do to prepare for the monthly maintenance?
To get live maintenance updates, including email alerts when maintenance begins and ends, go to the DigiCert Status page and select Subscribe to Updates.
Schedule high-priority orders, renewals, and reissues before or after the maintenance window.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
See the DigiCert Europe 2026 maintenance schedule for maintenance dates and times.
Services will be restored when maintenance is complete.
Upcoming scheduled global maintenance
DigiCert must perform critical maintenance on CertCentral during scheduled maintenance on June 6, 2026, from 22:00 – 24:00 MDT (June 7, 04:00 – 06:00 UTC).
Affected services
This maintenance affects CertCentral global.
It doesn’t affect our Certificate Issuing Service (CIS), Simple Certificate Enrollment Protocol (SCEP), or CertCentral Europe.
Service impact
CertCentral will be unavailable or experience service degradation for approximately 30 minutes total during the maintenance window. This unavailability or service degradation will happen in two 15-minute periods:
Part 1: Starting at 22:00 MDT / 04:00 UTC, CertCentral will be unavailable or experience service degradation for approximately 15 minutes.
Part 2: Starting at 22:45 MDT / 04:45 UTC, CertCentral will again be unavailable or experience service degradation for approximately 15 minutes
API impact
During the maintenance window, CertCentral APIs may return 503 Service Unavailable errors.
Requests that receive a 503 Service Unavailable error message must be submitted again when services are restored.
What can I do to prepare?
To get live maintenance updates, including email alerts when maintenance begins and ends, go to the DigiCert Status page and select Subscribe to Updates.
Schedule high-priority orders, renewals, and reissues before or after the maintenance window.
Expect interruptions if you use the CertCentral APIs for immediate certificate issuance and automated tasks.
See the DigiCert global 2026 maintenance schedule for maintenance dates and times.
June 1, 2026
Included in this update:
CertCentral: All public TLS certificates must be logged to CT logs
Starting June 1, 2026, DigiCert will log all public TLS certificates, including canaries and test certificates, to at least one certificate transparency (CT) log.
CT logging enforcement affects all DigiCert's public TLS certificates: DV, OV, EV, EU Qualified Website Authentication Certificate (QWAC), and EU QWAC PSD2, and all DigiCert brands: DigiCert®, GeoTrust®, Thawte®, RapidSSL®, and Encryption Everywhere®. Read our knowledge base article, DigiCert to Enforce CT Logging for All Public TLS Certificates.
Why is DigiCert enforcing CT logging for public TLS certificates?
To promote greater TLS certificate transparency and further enhance internet security, the Google Chrome Root Program Policy requires Certificate Authorities (CAs) begin logging all TLS certificates to at least one CT log by June 15, 2026. Learn more about the Google Chrome Root Program Policy.
Background
Until now, CT logging was required if a TLS certificate was intended for use in a browser such as Chrome. Non-logged certificates still worked in browsers but would provide untrusted warnings. With this new requirement, all public TLS certificates must be logged.
What must I do to prepare for the new CT logging requirement?
On June 1, 2026, DigiCert will log all your newly issued public TLS certificates to CT logs, including reissues and duplicates. The new CT log enforcement affects you if you currently keep TLS certificates out of CT logs.
By default, DigiCert logs all public TLS certificates to CT logs. Most DigiCert customers log all their public TLS certificates to CT logs.
Do you log all your public TLS certificates in CT Logs?
Yes, I log all public TLS certificates to CT logs. This change doesn’t affect you. No action is required. DigiCert will continue to log your TLS certificates to CT logs.
No, I keep some public TLS certificates out of CT logs. Then, this change affects you. DigiCert will start logging all your public TLS certificates to CT logs. See Removing the CT logging “opt out” options from CertCentral.
Action may be required depending on whether you need to keep TLS certificates out of CT logs from June 1, 2026, onward. CT log enforcement doesn’t affect your existing TLS certificates kept out of CT logs before June 1, 2026.
What if I’m unsure if a TLS certificate was logged to CT logs?
If you are unsure if you have a TLS certificate logged to CT logs, you can check them individually. You can also use the Report library to check whether your TLS certificates are logged in CT logs. Learn how to check if a TLS certificate was logged in CT logs.
What if I don't want my TLS certificates in CT logs?
Public trust: If your TLS certificates require public trust, they must be issued by a publicly trusted root hierarchy and logged in CT logs under the new Google Chrome policy. No exception.
Private trust: If your TLS certificates don't require public trust, you can use a private PKI hierarchy to keep your TLS certificates out of public CT logs beyond June 1, 2026. Private PKI hierarchies aren’t subject to Chrome's CT logging requirements because they don’t require public browser trust. To learn more about your private trust options, see the "What if I don't want to log my TLS certificates to CT logs" section of our knowledge base article.
Enforcing MPIC corroboration using four remote locations from two different regions
Starting June 1, 2026 and finishing no later than June 14, 2026, DigiCert will update our Multi-Perspective Issuance Corroboration (MPIC) process to require corroboration from at least four remote network locations across at least two different Regional Internet Registry regions to comply with the next phase of the CA/Browser Forum MPIC requirements.
Learn more about how DigiCert is using MPIC to verify domain control and perform CAA checks.
CA/Browser Forum timelines | Number of distinct remote network perspectives used | Number of allowed non-corroborations1 |
|---|---|---|
Phase one: effective March 2025 | Check from multiple network locations. | Not applicable |
Phase two: effective September 2025 | Check from at least two remote network locations. | One non-corroboration is allowed. |
Phase three: effective February 2026 | Check from at least three remote network locations and from at least two different Regional Internet Registries (RIRs). | One non-corroboration is allowed. |
Phase four: effective June 2026 | Check from at least four remote network locations and from at least two different RIRs. | One non-corroboration is allowed. |
1When checking from two to five remote locations and RIRs, if more than one network perspective doesn't corroborate (return the same results as) the primary network’s details, DigiCert validation and certificate issuance can’t proceed. | ||
Recent changes
May 15, 2026
Included in this update:
DigiCert will revoke specific ICA certificates to transition multipurpose G2 and G3 roots to dedicated TLS root hierarchies
On May 15, 2026, DigiCert will revoke specific G2 and G3 intermediate CA (ICA) certificates. End-entity certificates issued by these ICAs won’t be revoked and remain active but must be replaced. If the ICA certificate in an end-entity certificate's trust chain is revoked, the end-entity certificate is considered not trusted or invalid.
ICA certificate being revoked on May 15, 2026* | Certificates issued from the ICA |
|---|---|
DigiCert Global CA G2 | Public TLS certificates |
DigiCert G2 SMIME RSA4096 SHA384 2024 CA1 | Public S/MIME certificates |
DigiCert Global G3 Code Signing ECC SHA384 2021 CA1 | Public code signing certificates |
DigiCert Global G3 Code Signing ECC P256 SHA384 2021 CA1 | Public code signing certificates |
DigiCert Global G3 Code Signing Europe ECC P-384 SHA384 2023 CA1 | Public code signing certificates |
*Note: To find your replacement ICA certificate, see the G2 and G3 ICA certificates being revoked and their affected end-entity certificates table in our article. | |
What do I need to do to prepare for the ICA certificate revocations?
Before May 15, 2026, reissue and replace your affected certificates:
TLS certificates
Reissue your affected TLS certificates using the new intermediate certificate, then replace the old ones. Learn more.
S/MIME certificates
Reissue your affected S/MIME certificates using the new intermediate certificate, then replace the old ones. Learn more.
Code Signing certificates
Check that your signatures are timestamped. Resign non-timestamped files and other file types as needed before the ICA certificate is revoked. Then reissue your affected code signing certificate using its new intermediate certificate. Learn more.
Why is DigiCert moving to dedicate TLS root hierarchies?
The Google Chrome Root Program requires Certificate Authorities (CAs) to use dedicated TLS root hierarchies for issuing public TLS certificates. This revocation is required to comply with the Google Chrome Root Program requirement and transition the DigiCert Global Root G2 and DigiCert Global Root G3 root hierarchies into dedicated TLS-only hierarchies. Learn more about DigiCert's transition to dedicated TLS root hierarchies.
DigiCert will revoke specific cross-signed root certificates to transition multipurpose G2 and G3 roots to dedicated TLS root hierarchies
On May 15, 2026, DigiCert will revoke two G5 cross-signed root certificates. End-entity certificates that chain to the G5 root as the trust anchor remain valid and trusted until they expire. However, if your certificate needs an alternative trust path from the cross-signed root, it will fail after the cross-signed root is revoked.
Cross-signed root being revoked on May 15, 2026* | Certificates that may be affected |
|---|---|
G3 Cross Signed DigiCert TLS ECC P384 Root G5 | Public TLS certificates |
G3 Cross Signed DigiCert CS ECC P384 Root G5 | Public code signing certificates |
*Note: To find your replacement cross-signed root certificate, see the G5 cross-signed roots being revoked and their affected end-entity certificates table in our article. | |
What do I need to do to prepare for the revocation of cross-signed root certificates?
If your end-entity certificate uses a cross-signed root that will be revoked, replace the cross-signed root CA certificate in the certificate trust chain before May 15, 2026.
TLS certificates
For your TLS certificate, open the G5 Intermediate CA file, take out the old cross-signed root, and add the new one. Learn more.
Code Signing certificates
For your code signing certificate, open the G5 Intermediate CA file, remove the old cross-signed root, and add the new one. Learn more.
Why do I need to replace the cross-signed root certificate?
DigiCert's G5 roots are newer and might not be as widely available as the G2 and G3 roots. Some older operating systems may not have the G5 roots in their trust stores. DigiCert recommends installing a DigiCert G5 cross-signed root CA certificate to ensure your certificates remain trusted, even if the new G5 root is missing from the trust store. Learn how to replace a cross-signed root certificate.
Why is DigiCert moving to dedicate TLS root hierarchies?
The Google Chrome Root Program requires Certificate Authorities (CAs) to use dedicated TLS root hierarchies for issuing public TLS certificates. This revocation is required to comply with the Google Chrome Root Program requirement and transition the DigiCert Global Root G2 and DigiCert Global Root G3 root hierarchies into dedicated TLS-only hierarchies. Learn more about DigiCert's transition to dedicated TLS root hierarchies.
May 12, 2026
Included in this update:
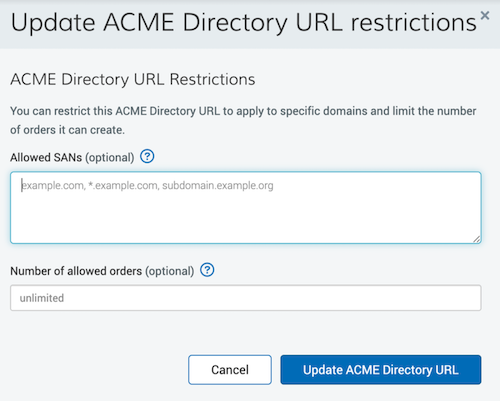
CertCentral ACME Directory URLs: Update domain and order limit restrictions
You can now update domain (SAN) and order limit restrictions for an existing ACME Directory URL. Before, you had to create a new ACME Directory URL to add or remove domains or increase the order limit.
What's new
After creating an ACME Directory URL, you can now:
Add or remove allowed SANs (domains)
Increase the number of allowed orders
Return the ACME Directory URL to unlimited status.
Important constraints:
Maximum of 250 SANs per ACME Directory URL
Order limit can be decreased if you haven’t already reached the limit
How to update SANs and order limit restrictions
Instructions apply to CertCentral Enterprise, Partner, and legacy retail accounts.
In CertCentral, in the left menu, go to Automation > ACME Directory URLs.
On the ACME Directory URLs page, in the Actions menu for the URL, select Update ACME Directory URL.
In the Update ACME Directory URL restrictions window, update the restrictions as needed:
Under Allowed SANs (optional), add or remove SANs (domains).
Under Number of allowed orders (optional), you can:
Increase the number of allowed orders.
Decrease the number of allowed orders if you haven’t already reached the limit.
Remove the existing limit and return the ACME Directory URL to unlimited status.
When ready, select Update ACME Directory URL.
References
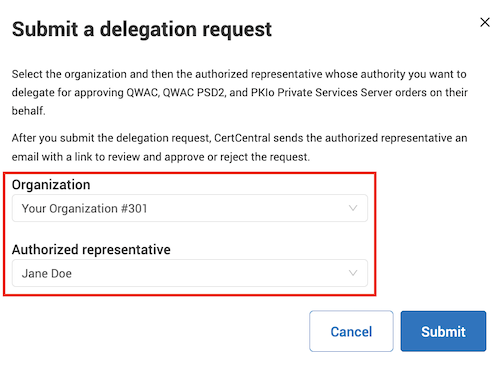
CertCentral Europe: Automated Authorized Representative Delegation for PKIo Private Services Server certificates
DigiCert has introduced an automated authorized representative delegation process in CertCentral Europe for PKIo Private Services Server certificates.
This feature allows certificates to be issued immediately when required domain and organization validation is complete.
How it works
DigiCert validates an authorized representative to approve PKIo Private Services Server certificate orders for your organization.
You submit a delegation request for a user or service user.
The representative completes a one-time approval.
When approved, PKIo Private Services Server certificate orders are automatically approved when the delegated approver includes the authorized representative in the order.
Benefits
Eliminates repeated manual approvals for each certificate order
Enables multiple certificate requests via CertCentral Europe or the Services API
Compliant with authorization requirements
Important notes:
Authorized representatives can delegate their authority to:
Administrators
Managers
Service users
Certificate orders must include the authorized representative to receive automatic approval.
Try it
In CertCentral Europe, in the left menu, go to Account > Users.
On the Users page, select a user.
On the user details page, under Authorized representative delegation, select Request authority delegation.
In the Submit a delegation request window, select an organization and an authorized representative.
When ready, select Submit.
Submitting a delegation request sends an email to the authorized representative.
References
May 9, 2026
Included in this update:
Upcoming scheduled Europe maintenance
DigiCert will perform scheduled maintenance on May 9, 2026, 17:00 - 19:00 CEST (15:00 - 17:00 UTC).
How does scheduled maintenance affect my CertCentral Europe services?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn how maintenance affects other DigiCert services, such as DigiCert ONE in our Netherlands location and the QuoVadis PrimoSign signing service, see the May 9 entry in the DigiCert Europe 2026 maintenance schedule.
What can I do to prepare for the monthly maintenance?
To get live maintenance updates, including email alerts when maintenance begins and ends, go to the DigiCert Status page and select Subscribe to Updates.
Schedule high-priority orders, renewals, and reissues before maintenance begins or when maintenance is complete.
Expect interruptions if you use the APIs (application programming interfaces) for immediate certificate issuance and automated tasks.
See the DigiCert Europe 2026 maintenance schedule for maintenance dates and times.
Services will be restored when maintenance is complete.
Upcoming scheduled global maintenance
DigiCert will perform scheduled maintenance on May 9, 2026, 22:00 – 24:00 MDT (May 10, 04:00 - 06:00 UTC).
How does scheduled maintenance affect my CertCentral services?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn how maintenance affects other DigiCert services, such as DigiCert ONE in our India location, see the May 9 entry in the DigiCert global 2026 maintenance schedule.
What can I do to prepare for the monthly maintenance?
To get live maintenance updates, including email alerts when maintenance begins and ends, go to the DigiCert Status page and select Subscribe to Updates.
Schedule high-priority orders, renewals, and reissues before maintenance begins or when maintenance is complete.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
See the DigiCert global 2026 maintenance schedule for maintenance dates and times.
Services will be restored when maintenance is complete.
May 1, 2026
Part 2: DigiCert to stop including the Client Authentication EKU in public TLS certificates
To learn more about part 1, see our October 1, 2025 change log entry,
Warning
Important update: Google Chrome updated their root program requirements and extended the timeline for removing the Client Authentication extended key usage (EKU) from public TLS certificates.
DigiCert will continue to include Client Authentication EKU in public TLS certificates until March 1, 2027. See our March 1, 2027, entry.
April 11, 2026
Included in this update:
Upcoming scheduled Europe maintenance
DigiCert will perform scheduled maintenance on April 11, 2026, 17:00 - 19:00 CEST (15:00 - 17:00 UTC).
How does scheduled maintenance affect my CertCentral services?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn how maintenance affects other DigiCert services, such as QuoVadis PrimoSign signing services and Document Trust Manager, see the April 11 entry in the DigiCert Europe 2026 maintenance schedule.
What can I do to prepare for the monthly maintenance?
Schedule high-priority orders, renewals, and reissues before maintenance begins or when maintenance is complete.
Expect interruptions if you use the APIs (application programming interfaces) for immediate certificate issuance and automated tasks.
To get live maintenance updates, including email alerts when maintenance begins and ends, go to the DigiCert Status page and select Subscribe to Updates.
See the DigiCert Europe 2026 maintenance schedule for maintenance dates and times.
Services will be restored when maintenance is complete.
Upcoming scheduled global maintenance
DigiCert will perform scheduled maintenance on April 11, 2026, 22:00 – 24:00 MDT (April 12, 04:00 - 06:00 UTC).
How does scheduled maintenance affect my CertCentral services?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
What can I do to prepare for the monthly maintenance?
Schedule high-priority orders, renewals, and reissues before maintenance begins or when maintenance is complete..
Expect interruptions if you use the APIs (application programming interfaces) for immediate certificate issuance and automated tasks.
To get live maintenance updates, including email alerts when maintenance begins and ends, go to the DigiCert Status page and select Subscribe to Updates.
See the DigiCert global 2026 maintenance schedule for maintenance dates and times.
Services will be restored when maintenance is complete.
March 24, 2026
CertCentral Webhooks: Added two new event types
We updated the CertCentral webhooks to send notifications for two new event types: description:
Order approval sent
CertCentral sends the "order approval sent" (
order_approval_email_sent) event when the approval email has been sent to all specified recipients.Order approval completed
CertCentral sends the "order approval completed" (
order_approval_complete) event when a recipient approves the order.
Subscribe to these events when creating or updating a webhook in CertCentral. Learn more about CertCentral event types.
March 17, 2026
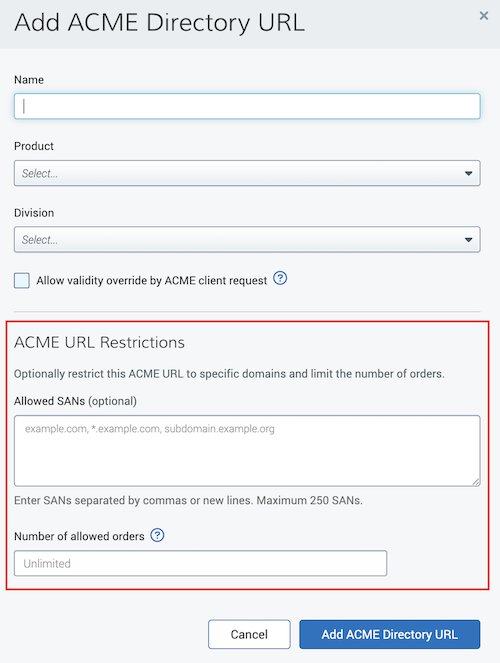
CertCentral ACME Directory URLs: Adding support for domain and order limit restrictions
We added two new ACME Directory URL features: restrict allowed domains and set order limits.
Allowed SANs (optional)
This feature allows administrators to limit requests to specific domains. Enter the domains (subject alternative names (SANs) and wildcards (*.your-domain)) that you can include in certificates using this ACME Directory URL.
Number of allowed orders
This feature helps administrators manage and monitor certificate issuance activity. Specify the number of orders that you can place using this ACME Directory URL. For unlimited orders, leave the field blank.
Background
Before we added these features, you could use an ACME Directory URL to order as many certificates as you wanted for any domain. This made it hard to control which domains could be included in an order and how many certificates were requested.
See for yourself (CertCentral Enterprise/Partner/Legacy Retail)
In CertCentral's left menu, go to Automation > ACME Directory URLs.
On the ACME Directory URLs page, under the page title, select the Add ACME Directory URL link.
Reference
March 10, 2026
DigiCert: Adding new dedicated IPv4 and IPv6 addresses
On March 10, 2026, at 10:00 MDT (16:00 UTC), DigiCert will add more dedicated IPv4 addresses and assign new dedicated IPv6 addresses for specific services.
To learn more about these IPv4 and IPv6 addresses, see our knowledge base article, DigiCert Certificate Status IP Addresses.
What do I need to do to prepare for the new dedicated IP addresses?
Does your company use allowlists to control outgoing traffic? Does your company support or plan to support IPv6 addresses?
If you don’t use allowlists, no action is required. Your DigiCert services will continue to work as they did before we added the IPv4 and IPv6 addresses.
If you use allowlists, update your allowlists as required to support your company’s IP addresses needs.
Make sure to include the new IP addresses before March 10, 2026, to keep your DigiCert services running as they were before we added these IP addresses.
Affected platforms:
CertCentral
CertCentral Europe
DigiCert ONE United States, Netherlands, Switzerland, Australia, and Japan instances*
QuoVadis® Trustlink
PKI Platform 8
Warning
*If your Trust Lifecycle Manager, Software Trust Manager, or Document Trust Manager (United States, Switzerland, Netherlands, Australia, or Japan) uses public certificates from CertCentral, CertCentral Europe, or PKI Platform 8, you may want to add these IP addresses to your allowlist.
OCSP or CRL distribution endpoints using any of the following subdomains aren’t affected:
one.digicert.com
one.nl.digicert.com
one.ch.digicert.com
one.au.digicert.com
one.digicert.co.jp
one.oracle.digicert.com
March 7, 2026
Included in this update:
Upcoming scheduled Europe maintenance
DigiCert will perform scheduled maintenance on March 7, 2026, 17:00 - 19:00 CET (16:00 - 18:00 UTC).
How does scheduled maintenance affect my CertCentral services?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn how maintenance affects other DigiCert services, such as the ADSS and QuoVadis PrimoSign signing services, see the March 7 entry in the DigiCert Europe 2026 maintenance schedule.
What can I do to prepare for the monthly maintenance?
Schedule high-priority orders, renewals, and reissues before maintenance begins or when maintenance is complete.
Expect interruptions if you use the APIs (Application Programming Interfaces) for immediate certificate issuance and automated tasks.
To get live maintenance updates, including email alerts when maintenance begins and ends, go to the DigiCert Status page and select Subscribe to Updates.
See the DigiCert Europe 2026 maintenance schedule for maintenance dates and times.
Services will be restored when maintenance is complete.
Upcoming scheduled global maintenance
DigiCert will perform scheduled maintenance on March 7, 2026, 22:00 – 24:00 MST (March 8, 05:00 - 07:00 UTC).
How does scheduled maintenance affect my CertCentral services?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
What can I do to prepare for the monthly maintenance?
Schedule high-priority orders, renewals, and reissues before maintenance begins or when maintenance is complete.
Expect interruptions if you use the APIs (Application Programming Interfaces) for immediate certificate issuance and automated tasks.
To get live maintenance updates, including email alerts when maintenance begins and ends, go to the DigiCert Status page and select Subscribe to Updates.
See the DigiCert global 2026 maintenance schedule for maintenance dates and times.
Services will be restored when maintenance is complete.
March 3, 2026
Included in this update:
Validating DNSSEC when verifying domain control and performing CAA checks
Notice
Important update: DigiCert will now start validating DNSSEC when verifying domain control and performing CAA checks on March 3, 2026. We originally planned this for February 24, 2026.
On March 3, 2026, DigiCert will start validating domain name system security extensions (DNSSEC), if present, when verifying domain control and performing DNS Certification Authority Authorization (CAA) checks. This change affects all products requiring domain validation and those requiring CAA checks before certificate issuance, such as public TLS and Secure Email (S/MIME) certificates.
Note: The use of DNSSEC isn’t mandatory. You don’t need to configure DNSSEC for DigiCert to issue a certificate. This information applies to those using or planning to use DNSSEC.
To learn more about this change and how it may affect you, read our knowledge base article, DigiCert to Validate DNSSEC to with Domain Control Validation and CAA Checks.
Why is DigiCert validating DNSSEC when verifying domain control and performing CAA checks?
DigiCert will start validating DNSSEC when verifying domain control and performing DNS CAA checks to align with the CA/Browser Forum’s Ballot SC-085v2: Require Validation of DNSSEC (when present) for CAA and DCV Lookups. This ballot requires Certificate Authorities (CAs) to validate DNSSEC, if present, for domain control to be verified, for CAA checks to pass, and for a certificate to be issued.
CertCentral: New DNSSEC error and status for domain validation and CAA checks
Starting March 3, 2026, DigiCert must validate DNSSEC if it’s configured for your domain during domain control validation and DNS Certification Authority Authorization (CAA) checks. To learn more about this change and how it may affect you, read our knowledge base article, DigiCert Validating DNSSEC when Verifying Domain Control and Performing CAA Checks.
What happens if DigiCert is unable to validate DNSSEC?
If DigiCert detects issues during DNSSEC validation, we’ll return the following error and status messages in CertCentral on the pending order details page. We’ll also return the error and status messages via the Services API for certificate requests that meet a specific use case.
DNSSEC Error
In CertCentral, on the order details page, we’ll return the following error and message when we detect issues in a domain's DNSSEC configuration that prevent DigiCert from finishing a domain's validation or CAA check.
Error code
dns_sec_validation_errorError message
We detected a DNSSEC validation issue on your domain. Please contact your DNS provider to review the configuration. If the record is not correctly configured, your provider may recommend correcting the configuration or temporarily removing DNSSEC until it can be properly reconfigured.
API use case for returning the DNSSEC error
Immediate certificate issuance with
"reject_if_pending": trueThe CertCentral Services API returns the
dns_sec_validation_errorfor certificate requests that qualify for immediate issuance and include the"reject_if_pending": trueflag.Notice
These types of requests will continue to be automatically rejected. As of March 3, we now also return a DNSSEC error to notify you that a DNSSEC issue is preventing immediate certificate issuance. Until the DNSSEC configuration issue is resolved, DigiCert can’t issue a certificate for a domain.
Immediate certificate issuance without
"reject_if_pending"For certificate requests that qualify for immediate issuance and don't include
"reject_if_pending", the CertCentral Services API returns a pending response as expected.
Checking the DNSSEC status in the Services API
For certificate requests placed via the Services API that return a pending response, use the Order validation status endpoint to check whether a DNSSEC issue is delaying your domain validation or certificate issuance.
Status code
DNS_SEC_VALIDATION_ERRORStatus message
We detected a DNSSEC validation issue on your domain. Please contact your DNS provider to review the configuration. If the record is not correctly configured, your provider may recommend correcting the configuration or temporarily removing DNSSEC until it can be properly reconfigured.
February 24, 2026
Included in this update:
Shortening the organization validation reuse period for public OV TLS certificates to 397 days
Moving to 459-day validity for public code signing certificates
Enforcing MPIC corroboration using three remote locations from two different regions
Validating DNSSEC when verifying domain control and performing CAA checks
Moving to 199-day validity for public TLS certificates
On February 24, 2026, DigiCert will stop accepting public TLS certificate requests with a validity greater than 199 days. Also, all public TLS certificates issued on or after February 24, 2026, can’t exceed the new 199-day maximum validity.
Why is DigiCert reducing the maximum validity of public TLS certificates to 199 days?
DigiCert is moving to 199-day validity for public TLS certificates to align with the CA/Browser Forum’s Ballot SC081v3: Introduce Schedule of Reducing Validity and Data Reuse Periods. This ballot sets a timeline for all Certificate Authorities (CAs) to reduce TLS certificate validity from 398 days to 200 days in 2026, 100 days in 2027, and 47 days in 2029.
Learn more about Ballot SC081v3.
CA/Browser Forum | DigiCert | ||
Maximum certificate validity | Due date | Maximum certificate validity1 | Timeline |
398 days | Before March 15, 2026 | 397 days | Before February 24, 2026 |
200 days | Between March 15, 2026, and March 15, 2027 | 199 days | Between February 24, 2026, and early 20272 |
100 days | Between March 15, 2027, and March 15, 2029 | 99 days | Between early 2027 and early 20292 |
47 days | After of March 15, 2029 | 46 days | After early 20292 |
1DigiCert's maximum certificate validities are one day shorter than the maximum validity allowed by the CA/Browser Forum. We do this to avoid exceeding the maximum permitted validity. 2Future release dates are subject to change based on the latest CA/Browser Forum requirements. | |||
Shortening the domain validation reuse period to 199 days
On February 24, 2026, DigiCert will shorten the domain validation reuse period to 199 days. The reuse period for your existing domain validation will also be shortened to 199 days.
Why is DigiCert doing this?
DigiCert is shortening the domain validation reuse period to align with the CA/Browser Forum’s Ballot SC081v3: Introduce Schedule of Reducing Validity and Data Reuse Periods. This ballot sets a timeline to reduce the domain validation reuse period from 398 days to 200 days in 2026, 100 days in 2027, and 10 days in 2029.
Learn more about Ballot SC081v3.
CA/Browser Forum | DigiCert | ||
Maximum domain validation reuse period | Due date | Maximum domain validation reuse period1 | Timeline |
398 days | Before March 15, 2026 | 397 days | Before February 24, 2026 |
200 days | Between March 15, 2026, and March 15, 2027 | 199 days | Between February 24, 2026, and early 20272 |
100 days | Between March 15, 2027, and March 15, 2029 | 99 days | Between early 2027 and early 20292 |
10 days | After of March 15, 2029 | 9 days | After early 20292 |
1DigiCert’s maximum validation reuse period is set to one day less than the CA/Browser Forum’s allowed maximum period. We do this to ensure that we never exceed the permitted reuse window. 2Future release dates are subject to change based on the latest CA/Browser Forum requirements. | |||
Shortening the organization validation reuse period for public OV TLS certificates to 397 days
On February 24, 2026, DigiCert will shorten the organization validation reuse period for public OV TLS certificates from 825 days to 397 days. The reuse period for your existing 825-day OV organization validations will also be shortened.
Why is DigiCert doing this?
DigiCert is shortening the organization validation reuse period to align with the CA/Browser Forum’s Ballot SC081v3: Introduce Schedule of Reducing Validity and Data Reuse Periods, which reduces the OV organization validation reuse period to 398 days in 2026.
Learn more about Ballot SC081v3.
CA/Browser Forum | DigiCert | ||
Maximum OV organization validation reuse period | Due date | Maximum OV organization validation reuse period1 | Timeline |
825 days | Before March 15, 2026 | 825 days | Before February 24, 2026 |
398 days | After March 15, 2026 | 397 days | After February 24, 2026 |
1DigiCert’s maximum validation reuse period is set to one day less than the CA/Browser Forum’s allowed maximum period to ensure that we never exceed the permitted reuse window. | |||
Moving to 459-day validity for public code signing certificates
On February 24, 2026, DigiCert will stop accepting public code signing certificate requests with the validity greater than 459 days. Also, all public code signing certificates issued on or after February 24, 2026, can’t exceed the new 459-day maximum validity.
Learn more about the move to 459-day validity for public Code Signing certificates.
Why is DigiCert reducing the maximum validity of public code signing certificates to 459 days?
DigiCert is moving to 459-day validity for public code signing certificates to align with the CA/Browser Forum’s Ballot CSC-31: Maximum Validity Reduction. This ballot reduces code signing certificate validity from 39 months to 460 days (about 15 months) by March 1, 2026.
Learn more about Ballot CSC-31.
CA/Browser Forum | DigiCert | ||
Maximum certificate validity | Due date | Maximum certificate validity1 | Timeline |
39 months | Before March 1, 2026 | 39 months | Before February 24, 2026 |
460 days | After March 1, 2026 | 459 days | After February 24, 2026 |
1DigiCert's maximum certificate validities are one day shorter than the maximum validity allowed by the CA/Browser Forum, to avoid exceeding the maximum permitted validity. | |||
CertCentral: Retiring the legacy ACME service
On February 24, 2026, DigiCert will retire the legacy CertCentral ACME service. If you have any legacy ACME credentials in your account, you should see a banner message above the table on the ACME Directory URLs page in CertCentral.
“Some of your ACME credentials are for a previous version of the CertCentral ACME service. To use the latest ACME features, add new ACME credentials to replace the ones marked as legacy below.”
To help identify your legacy ACME credentials, we added a warning icon next to each affected credential's status in the Status column on the ACME Directory URLs page. In the CertCentral menu, go to Automation > ACME Directory ULRs.
What do I need to do?
Requests to legacy ACME URLs will fail to issue a certificate starting February 24, 2026. If you have any active legacy ACME credentials, you need to replace them with credentials for the new CertCentral ACME service before February 24.
To replace your legacy ACME credentials:
On the ACME Directory URLs page, create new ACME credentials for each legacy ACME credential.
To view your legacy ACME credential’s products and settings, select the help icon (question mark) next to its description. You can reference these details when creating your new, replacement ACME credentials to ensure consistency.
Update your ACME clients.
Follow the software provider’s guidelines to update each ACME client with the newly created ACME URL and external account binding credentials.
References
CertCentral Services API integrations
Update API integrations before February 24, 2026. Stop using the ACME External Account Binding - legacy endpoint and start using the ACME External Account Binding - new endpoint.
Why is DigiCert retiring the legacy CertCentral ACME service?
The new version of the CertCentral ACME service offers significant upgrades over the legacy version, including:
Support for DV TLS products
ACME domain control validation for all TLS products
Dynamic detection logic (see ACME automation actions)
Learn more about the latest CertCentral ACME automation features.
Enforcing MPIC corroboration using three remote locations from two different regions
Starting February 24, 2026, DigiCert will update our Multi-Perspective Issuance Corroboration (MPIC) process to enforce corroboration using at least three remote network locations from at least two different Regional Internet Registry regions to comply with the next phase of CA/Browser Forum MPIC requirements.
Learn more about how DigiCert is using MPIC to verify domain control and perform CAA checks.
On February 24, 2026, DigiCert will add another User Agent and two new IP addresses to the MPIC agents' IP addresses. If you’re using the HTTP Practical Demonstration method to validate your domains, make sure to review the Add User Agents DigiCert DCV /1.1 and DigiCert DCV Bot/1.1 or IP addresses to your allowlist section in our knowledge base article.
CA/Browser Forum Timelines | Number of Distinct Remote Network Perspective Used | Number of Allowed Non-corroborations |
|---|---|---|
Phase one: effective March 2025 | Check from multiple network locations. | Not applicable |
Phase two: effective September 2025 | Check from at least two remote network locations. | One non-corroboration allowed.1 |
Phase three: effective February 2026 | Check from at least three remote network locations and from at least two different Regional Internet Registries (RIRs). | One non-corroboration allowed.1 |
1When checking from two to five remote locations and RIRs, if more than one network perspective doesn't corroborate (return the same results as) the primary network’s details, DigiCert validation and certificate issuance can’t proceed. | ||
Validating DNSSEC when verifying domain control and performing CAA checks
Warning
Important update: DigiCert has postponed validating DNSSEC when verifying domain control and performing CAA checks until March 3, 2026. See our March 3, 2026, entry.
February 7, 2026
Included in this update:
Upcoming scheduled Europe maintenance
DigiCert will perform scheduled maintenance on February 7, 2026, 17:00 - 19:00 CET (16:00 - 18:00 UTC).
How does scheduled maintenance affect my CertCentral services?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn how maintenance affects other DigiCert services, such as the ADSS and QuoVadis PrimoSign signing services and Document Trust Manager, see the February 7 entry in the DigiCert Europe 2026 maintenance schedule.
What can I do to prepare for the monthly maintenance?
Schedule high-priority orders, renewals, and reissues begins or when maintenance is complete.
Expect interruptions if you use the APIs (Application Programming Interfaces) for immediate certificate issuance and automated tasks.
To get real-time maintenance updates, including email alerts when maintenance begins and ends, go to the DigiCert Status page and select Subscribe to Updates.
See the the DigiCert Europe 2026 maintenance schedule for maintenance dates and times.
Services will be restored when maintenance is complete.
Upcoming scheduled global maintenance
DigiCert will perform scheduled maintenance on February 7, 2026, 22:00 – 24:00 MST (February 8, 05:00 - 07:00 UTC).
How does scheduled maintenance affect my CertCentral services?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn how maintenance affects other DigiCert services, such as Document Trust Manager’s PrimoSign signing service, see the February 7 entry in the DigiCert global 2026 maintenance schedule.
What can I do to prepare for the monthly maintenance?
Schedule high-priority orders, renewals, and reissues before maintenance begins or when maintenance is complete.
Expect interruptions if you use the APIs (Application Programming Interfaces) for immediate certificate issuance and automated tasks.
To get real-time maintenance updates, including email alerts when maintenance begins and ends, go to the DigiCert Status page and select Subscribe to Updates.
See the DigiCert global 2026 maintenance schedule for maintenance dates and times.
Services will be restored when maintenance is complete.
January 15, 2026
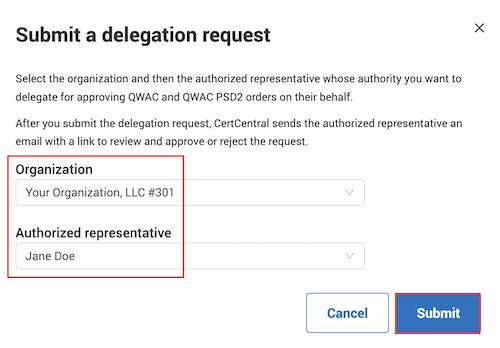
CertCentral Europe: Automated authorized representative approval for QWAC and QWAC PSD2 certificates
In CertCentral Europe, DigiCert has created an automated process for delegating authorized representatives for Qualified Website Authentication Certificates (QWAC) and QWAC PSD2. This process allows you to issue these certificates immediately when required validation and confirmation of the payment service provider roles (for QWAC PSD2) is finished.
How does the delegation process work?
First, DigiCert must validate an authorized representative to approve QWAC and QWAC PSD2 certificates for an organization. Then, in CertCentral, you can request that the authorized representative delegate their approval authorization for the organization to a CertCentral Administrator, Manager, or Service user.
The authorized representative performs a one-time approval delegation via email. Then CertCentral automatically applies the representative’s approval to all QWAC and QWAC PSD2 orders submitted by the associated CertCentral User or Service User.
Benefits
This delegated approval streamlines certificate issuance eliminating the need for repeated individual approvals for every QWAC and QWAC PSD2 order. You can now request multiple QWAC and QWAC PSD2 certificates in CertCentral Europe or via the CertCentral Services API while maintaining compliance with authorization requirements.
Items to note
Authorized representatives can delegate their authority to CertCentral Administrators and Managers. They can't delegate authority to Finance Managers, Standard Users, and Limited Users.
A service user has API-only access to your CertCentral account. You must be an administrator to create service users. When creating a service user, you link the administrator's permissions to the key.
When ordering QWAC and QWAC PSD2 certificates, the delegated approver must include the authorized representative who delegated their approval authority to them in the order. If they don't, the order doesn't receive an automatic approval.
Authority delegation instructions
See for yourself
In CertCentral Europe, in the left menu, go to Account > Users.
On the Users page, select the user you want the authorized representative to delegate their approval authority to.
On the user details page, under Authorized representative delegation, select Request authority delegation.
In the Submit a delegation request window, select an organization validated for QWAC and QWAC PSD2 certificates and an authorized representative for the organization.
January 13, 2026
Included in this update:
CertCentral displays 199-day domain validation reuse expiration dates
On January 13, 2026, CertCentral began displaying the 199-day domain expiration date alongside the current 397-day expiration date to help you identify the affected domains.
On the Domains page in CertCentral, we added a new Validation expires SC-081 column next to the Validation expires column. This new column allows you to compare the original and new expiration dates and determine whether domain revalidation is required.
On the “domain’s detail” page in CertCentral, we added a new Validation expires SC-081 field next to the Validation expires field. The new field lets you easily compare the original and new expiration dates and plan domain revalidation as needed. At the bottom of the domain detail page, you can initiate domain revalidation if the shortened domain expiration date expires on February 24, 2026.
See for yourself
In CertCentral, in the left main menu, go to Certificates > Domains.
On the Domains page, in the Validation status menu, select Completed / Validated and then select Go.
This filter allows you to view domains with active validations.
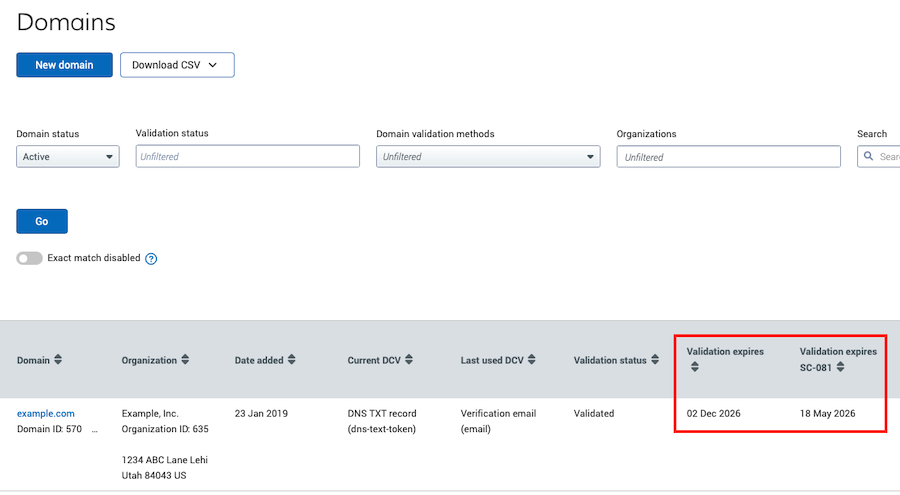
In the Validation expires SC-081 column, use the up and down arrows to filter the expiration dates.
To download a CSV file, select Download CSV > Download Filtered Records under Domains (page title).
Note: CSV files have a limit of 1,000 records.
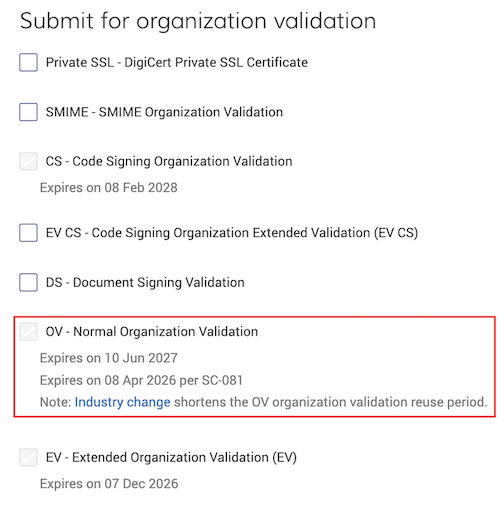
CertCentral displays 397-day OV organization validation reuse expiration dates
On January 13, 2026, CertCentral began displaying the 397-day OV organization expiration date alongside the current 825-day OV organization expiration date to help you identify affected organizations.
On the organization detail page in CertCentral, we added a second OV organization expiration date to comply with Ballot SC-81 requirements for a 397-day OV organization reuse period. This second expiration date allows you to easily compare the original and new expiration dates and plan for organization revalidation as needed.
See for yourself
In CertCentral, in the left main menu, go to Certificates > Organizations.
On the Organizations page, in the Validated for column, select an organization name validated for OV.
On the organization’s details page, under Submit for organization validation, find OV – Normal Organization Validation.
You should see "Expires on {{date}}" per SC-081" under "Expires on {{date}}".
January 10, 2026
Included in this update:
Upcoming scheduled Europe maintenance
DigiCert will perform scheduled maintenance on January 10, 2026, 17:00 - 19:00 CET (16:00 - 18:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn how maintenance affects other DigiCert services, such as the QuoVadis PrimoSign signing service and TrustLink Enterprise certificate issuance, see the January 10 entry in the DigiCert Europe 2026 maintenance schedule.
What can I do?
Schedule high-priority orders, renewals, and reissues begins or when maintenance is complete.
Expect interruptions if you use the APIs (Application Programming Interfaces) for immediate certificate issuance and automated tasks.
To get real-time maintenance updates, including email alerts when maintenance begins and ends, go to the DigiCert Status page and select Subscribe to Updates.
See the DigiCert Europe 2026 maintenance schedule for maintenance dates and times.
Services will be restored when maintenance is complete.
Upcoming scheduled global maintenance
DigiCert will perform scheduled maintenance on January 10, 2026, 22:00 – 24:00 MST (January 11, 05:00 - 07:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn how maintenance affects other DigiCert services, such as Document Trust Manager’s PrimoSign signing service, see the January 10 entry in the DigiCert global 2026 maintenance schedule.
What can I do?
Schedule high-priority orders, renewals, and reissues begins or when maintenance is complete.
Expect interruptions if you use the APIs (Application Programming Interfaces) for immediate certificate issuance and automated tasks.
To get real-time maintenance updates, including email alerts when maintenance begins and ends, go to the DigiCert Status page and select Subscribe to Updates.
See the DigiCert global 2026 maintenance schedule for maintenance dates and times.
Services will be restored when maintenance is complete.
December 8, 2025
DigiCert 2026 maintenance schedules
DigiCert has published the 2026 maintenance schedules to help you plan your certificate, services, and platform activities. We update these schedules as we get more information on how maintenance affects your DigiCert services.
Maintenance schedules
With customers worldwide, we understand there’s no best time for everyone. However, after reviewing customer usage data, we selected times that would affect the fewest customers.
Maintenance schedule guidelines and what to expect:
Maintenance is scheduled for the first weekend of each month unless otherwise noted.
Each maintenance window is scheduled for a duration of two hours.
Although we have redundancies to protect your service, some DigiCert services may be temporarily unavailable.
Normal operations resume when the maintenance is finished.
To get live maintenance updates, subscribe to the DigiCert Status page. Your subscription includes email alerts for when maintenance begins and when it ends.
If you have questions or require more information about these maintenance windows, contact your account manager or DigiCert Support.
December 6, 2025
Included in this update:
Upcoming scheduled Europe maintenance
DigiCert will perform scheduled maintenance on December 6, 2025, 17:00 - 19:00 CET (16:00 - 18:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn how maintenance affects other DigiCert services, such as the QuoVadis PrimoSign and SealSign signing services, see the December 6 entry in the DigiCert Europe 2025 maintenance schedule.
What can I do?
To minimize disruption, consider the following recommendations:
Complete high-priority orders, renewals, and reissues before maintenance begins or wait until maintenance is complete.
If using APIs for immediate certificate issuance or automation, schedule these operations outside the maintenance window. If you must perform time-sensitive API operations during the downtime, you may experience interruptions to immediate certificate issuance and automated tasks.
To get real-time maintenance updates, including email alerts when maintenance begins and ends, go to the DigiCert Status page and select Subscribe to Updates.
To review the Europe maintenance windows dates and times, go to DigiCert Europe 2025 maintenance schedule.
Services are restored when the maintenance is finished.
Upcoming scheduled global maintenance
Parts of DigiCert’s public certificate issuance process, account creation, and individual and organization validation will be down for approximately 2 minutes while we work on our organization and individual validation services during scheduled global maintenance on December 6, 2025, 22:00 – 24:00 MST (December 7, 2025, 05:00 – 07:00 UTC). For more details on the two-minute downtime, see the December 6 entry in the 2025 global maintenance schedule.
Notice
Immediate certificate issuance not affected
The work on our organization and individual validation services doesn’t affect DigiCert’s immediate certificate issuance process.
If your organization and domain validations are current, DigiCert immediately issues your certificate.
How does this affect me?
The work on our organization and individual validation services begins at 22:00 MST (05:00 UTC). At this time, the following DigiCert services will be down for approximately 2 minutes:
Public certificate requests: Can’t submit a certificate request for a new organization, an organization with expired validation, or a new individual.
Organization validation: Can’t add or submit an organization for validation.
Individual validation: Can’t add a new individual.
Account creation: Can’t create a CertCentral account: Enterprise, Partner, and Subscription.
Affected platforms and APIs: CertCentral, CertCentral Services API, and Certificate Issuing Service (CIS).
Notice
CertCentral Europe and its Services API aren’t affected.
Affected certificates:
OV and EV TLS
Code signing and EV code signing
Secure Email for Employee and Organization
Document Signing for Individual, for Employee, and for Organization
Client
Notice
DV and Secure Email for Individual Mailbox certificates aren’t affected.
What can I do?
To minimize disruption, consider the following recommendations:
Complete high-priority orders, renewals, and reissues before maintenance begins or wait until maintenance is complete.
If using APIs for immediate certificate issuance or automation, schedule these operations outside the maintenance window. If you must perform time-sensitive API operations during the downtime, you may experience interruptions to immediate certificate issuance and automated tasks.
To get real-time maintenance updates, including email alerts when maintenance begins and ends, go to the DigiCert Status page and select Subscribe to Updates.
To review the global maintenance windows dates and times, go to DigiCert Global 2025 maintenance schedule.
Services are restored when the maintenance is finished.
Acronyms used in the change log entry: Organization validation (OV), extended validation (EV), Transport Security Layer (TLS), Application Programming Interface (API)
November 13, 2025
DigiCert ACME Client now available in CertCentral
As certificate lifespans shrink from 397 days to just 46, now is the perfect time to automate your TLS certificate process and stay ahead of industry changes. (Learn more about the upcoming industry change.)
Introducing the new DigiCert ACME Client, a tool designed to simplify certificate installation and management, while giving advanced users the flexibility they need.
One-line deployment: Quickly deploy the DigiCert ACME Client on both Linux and Windows systems with a single command, streamlining the installation and setup process.
Optimized installation process: The installer now intelligently detects existing installations to avoid redundant downloads and enables immediate command execution, resulting in faster start up.
Intelligent default configuration: A built-in default configuration system minimizes the required setup options while maintaining secure and reliable defaults.
Advanced configuration system: Added support for persistent settings, intelligent defaults, and flexible configuration management. This system reduces the need for command-line arguments while offering comprehensive control over all aspects of certificate management.
Documentation: Full documentation available here: https://automation-service.digicert.com/dc-acme/dc-acme.html.
CertCentral Subscription accounts
In addition to the DigiCert ACME Client, CertCentral Subscription accounts now feature a brand-new Automation interface. (Learn how to identify your CertCentral account).
The new interface:
Supports the DigiCert ACME Client and Certbot.
Supports Windows, Linux, and other systems
Supports Apache, Windows, Nginx, and other servers
Simplifies deployment and installation by generating customized commands tailored to your operating system, server type, and environment.
November 8, 2025
Included in this update:
Upcoming scheduled Europe maintenance
DigiCert will perform scheduled maintenance on November 8, 2025, 17:00 - 19:00 CET (16:00 - 18:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn how maintenance affects other DigiCert services, such as the QuoVadis PrimoSign service, see the November 8 entry in the DigiCert Europe 2025 maintenance schedule.
What can I do?
Plan accordingly:
Schedule high-priority orders, renewals, and reissues begins or when maintenance is complete.
Expect interruptions if you use the APIs (Application Programming Interfaces) for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts that notify you when maintenance begins and ends.
See the DigiCert Europe 2025 maintenance schedule for maintenance dates and times.
Services are restored when the maintenance is finished.
Upcoming scheduled Global maintenance
DigiCert will perform scheduled maintenance on November 8, 2025, 22:00 – 24:00 MST (November 9, 2025, 05:00 – 07:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
What can I do?
Plan accordingly:
Schedule high-priority orders, renewals, and reissues before maintenance begins or when maintenance is complete.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts that notify you when maintenance begins and ends.
See the DigiCert Global 2025 maintenance schedule for maintenance dates and times.
Services are restored when the maintenance is finished.
November 3, 2025
DigiCert moving to new dedicated IP addresses for api.digicert.com
On November 3, 2025, at 10:00 MDT (16:00 UTC), DigiCert will assign four new IP addresses to api.digicert.com. For information, see our knowledge base article, DigiCert IP addresses for api.digicert.com.
Notice
Important update: DigiCert has postponed assigning the new dedicated addresses to api.digicert.com until November 3, 2025. We originally planned this work for October 27, 2025.
What do I need to do to prepare for the new dedicated IP addresses?
Do you use the Direct Cert Portal API or CertCentral Services API?
Do you use api.digicert.com for these API (application programming interface) integrations or any third-party tools/services that use api.digicert.com?
Do you use allowlists to control incoming and outgoing connectivity to your environment?
If you don’t use api.digicert.com for any API integrations, or if you do use api.digicert.com but don’t use allowlist, no action is required.
If you replied yes to all three questions, then action is required. Add the new IP addresses to your allowlist by November 3, 2025. Updating your allowlist helps ensure that your api.digicert.com integrations continue to work as they did before DigiCert assigned the new IP addresses.
October 28, 2025
DigiCert CertCentral®: Consolidating supported CNAME record configurations
On October 28, 2025, you must use the static prefix _dnsauth CNAME record configuration to perform your DNS CNAME domain validation. DigiCert is ending support for the [random_value] prefix DNS CNAME record configuration
Static prefix
_dnsauthCNAME record configuration:In the hostname field (or equivalent), enter
_dnsauth.In the target host field (or equivalent), enter
[random_value].dcv.digicert.comto point the CNAME record to dcv.digicert.com.
Deprecating on October 28, 2025 –
[random_value]prefix CNAME record configuration:In the hostname field (or equivalent), enter the
[random_value].In the target host field (or equivalent), enter
dcv.digicert.comto point the CNAME record to dcv.digicert.com.
Beginning October 28, 2025, you must configure your DNS CNAME record with the static prefix _dnsauth to perform your CNAME record domain control validation (DCV). If you configure the CNAME record with the [random_value] prefix, DigiCert's CNAME record check will fail. Your domain won’t be validated, preventing DigiCert from issuing your certificate.
How does this change affect my existing domain validations done with the [random_value] prefix CNAME record configuration?
Domain validations done with the old variant ([random_value] prefix) before October 28, 2025, remain valid and can be reused to issue certificates until the domain validations expire.
However, when you revalidate these domains, you must use the new static prefix _dnsauth CNAME record configuration.
Why is DigiCert supporting just the static prefix _dnsauth CNAME record configuration?
DigiCert is deprecating the current system used for domain control validation (DCV) workflows and replacing it with our Open-Source Domain Control Validation code. As part of this effort, we’re simplifying DCV methods and eliminating some variants. Our Open Source DCV code has undergone independent review offering greater transparency and improved performance.
Resources
October 27, 2025
DigiCert moving to new dedicated IP addresses for api.digicert.com
On October 27, 2025, at 10:00 MDT (16:00 UTC), DigiCert will assign four new IP addresses to api.digicert.com. For information, see our knowledge base article, DigiCert IP addresses for api.digicert.com.
Warning
Important update: DigiCert has postponed assigning the new dedicated addresses to api.digicert.com until November 3, 2025. See our November 3, 2025, entry.
October 13, 2025
DigiCert's site seal service may be unavailable for several minutes
On October 13, 2025, from 19:30 to 20:00 MDT (October 14, 01:30 to 02:00 UTC), DigiCert will perform maintenance on our site seal service. During this time, DigiCert's site seal service may be unavailable for several minutes.
How does this affect me?
Do you display the DigiCert Smart Seal or one of the DigiCert brand site seals on your website?
If not, then this doesn't affect you.
If yes, then our Smart Seal and site seals may stop displaying on your website for several minutes on October 13.
What do I need to do?
Nothing. When we finish our work, your DigiCert Smart Seal, and DigiCert brand site seals should reappear on your website.
Need help?
If you have questions or concerns about the site seal downtime, contact your account manager or DigiCert Support.
October 11, 2025
Included in this update:
Upcoming scheduled Europe maintenance
DigiCert will perform scheduled maintenance on October 11, 2025, 17:00 - 19:00 CEST (15:00 - 17:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn about the impact of the October 11 maintenance on other DigiCert services, such as the ADSS signing service, see the Saturday, October 11 entry in the DigiCert Europe 2025 maintenance schedule.
What can I do?
Plan accordingly:
Schedule high-priority orders, renewals, and reissues before maintenance begins or when maintenance is complete.
Expect interruptions if you use the APIs (application programming interfaces) for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts that notify you when maintenance begins and ends.
See the DigiCert Europe 2025 maintenance schedule for maintenance dates and times.
Services are restored when the maintenance is finished.
Upcoming scheduled Global maintenance
DigiCert will perform scheduled maintenance on October 11, 2025, 22:00 – 24:00 MDT (October 12, 2025, 04:00 – 06:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
What can I do?
Plan accordingly:
Schedule high-priority orders, renewals, and reissues before maintenance begins or when maintenance is complete.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts that notify you when maintenance begins and ends.
See the DigiCert Global 2025 maintenance schedule for maintenance dates and times.
Services are restored when the maintenance is finished.
October 1, 2025
Part 1: DigiCert to stop including the Client Authentication EKU in public TLS certificates by default
Beginning October 1, 2025, DigiCert will stop including the Client Authentication extended key usage (EKU) in public TLS certificates by default and issue these certificates with just the Server Authentication EKU.
What do I need to do?
If using your TLS/SSL certificates solely for securing websites (HTTPS), then no action is required. However, DigiCert recommends reviewing your TLS certificate process to verify that it just includes securing websites.
If you use your public TLS certificates to authenticate clients to a server, such as users or devices, action is required. You can still include the Client Authentication EKU in your certificates until May 1, 2026. However, you must do so proactively while requesting a TLS certificate in CertCentral or via the CertCentral Services API (application programming interface).
DigiCert recently added new EKU options to our public TLS certificate process. These options allow you to include the Server Authentication and Client Authentication EKUs in your certificates. See the August 12, 2025, change log entry.
CertCentral Resources
Why is DigiCert going to stop including the client authentication EKU in public TLS certificates by default?
This change aligns with Google Chrome’s root program requirements to enhance security and promote interoperability. For more information about DigiCert's timeline for phasing out the Client Authentication EKU, read our article about sunsetting the client authentication EKU.
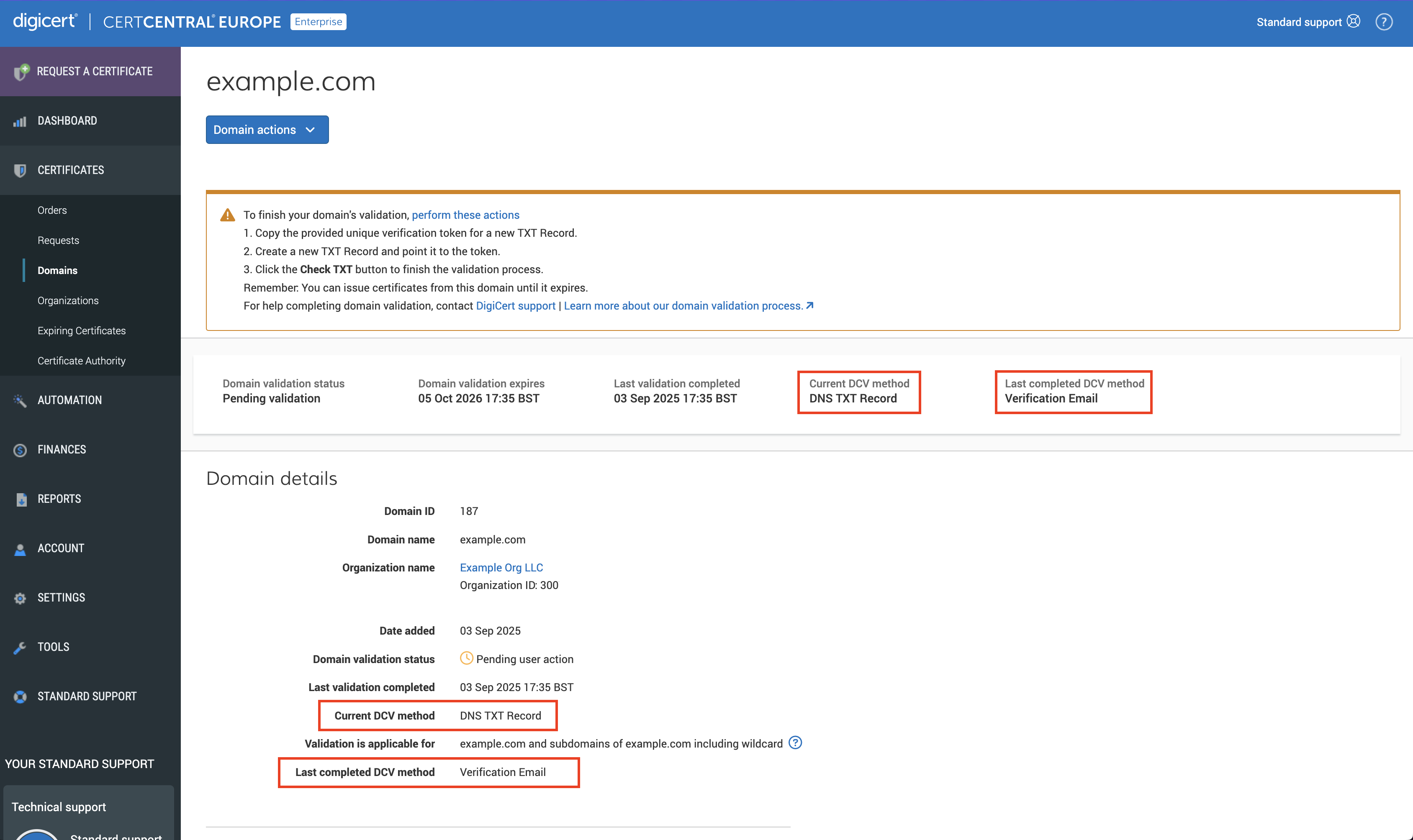
CertCentral: Improvements to the domain prevalidation process
In CertCentral, we updated the Domains and the domain details pages making it easier to discover the following domain control validation (DCV) information about each domain:
DCV method last used to validate the domain
DCV method currently submitted to validate the domain
Domains page
On the Domains page, we removed the DCV method column and replaced it with two new columns: Current DCV method and Last completed DCV method. Now, from the Domains page, you can quickly verify the last and current validation methods used to validate the domain.
Domain details page
On the domain details page, in the information panel and Domain details section, we removed the DCV method entry and replaced it with two entries: Current DCV method and Last completed DCV method. Now, when on the domain’s details page, quickly find the last DCV method and current DCV method used to validate the domain.
See for yourself
In CertCentral, in the left menu, go to Certificates > Domains.
For CertCentral Subscriptions accounts, in the left menu, go to Validation > Domains.
On the Domains page, you now see the two new columns: Current DCV method and Last completed DCV method.
In the Domain name column, select a domain link.
On the domain details page, in the information panel and the Domain details section, you now see the new entries: Current DCV method and Last completed DCV method.
Domains page
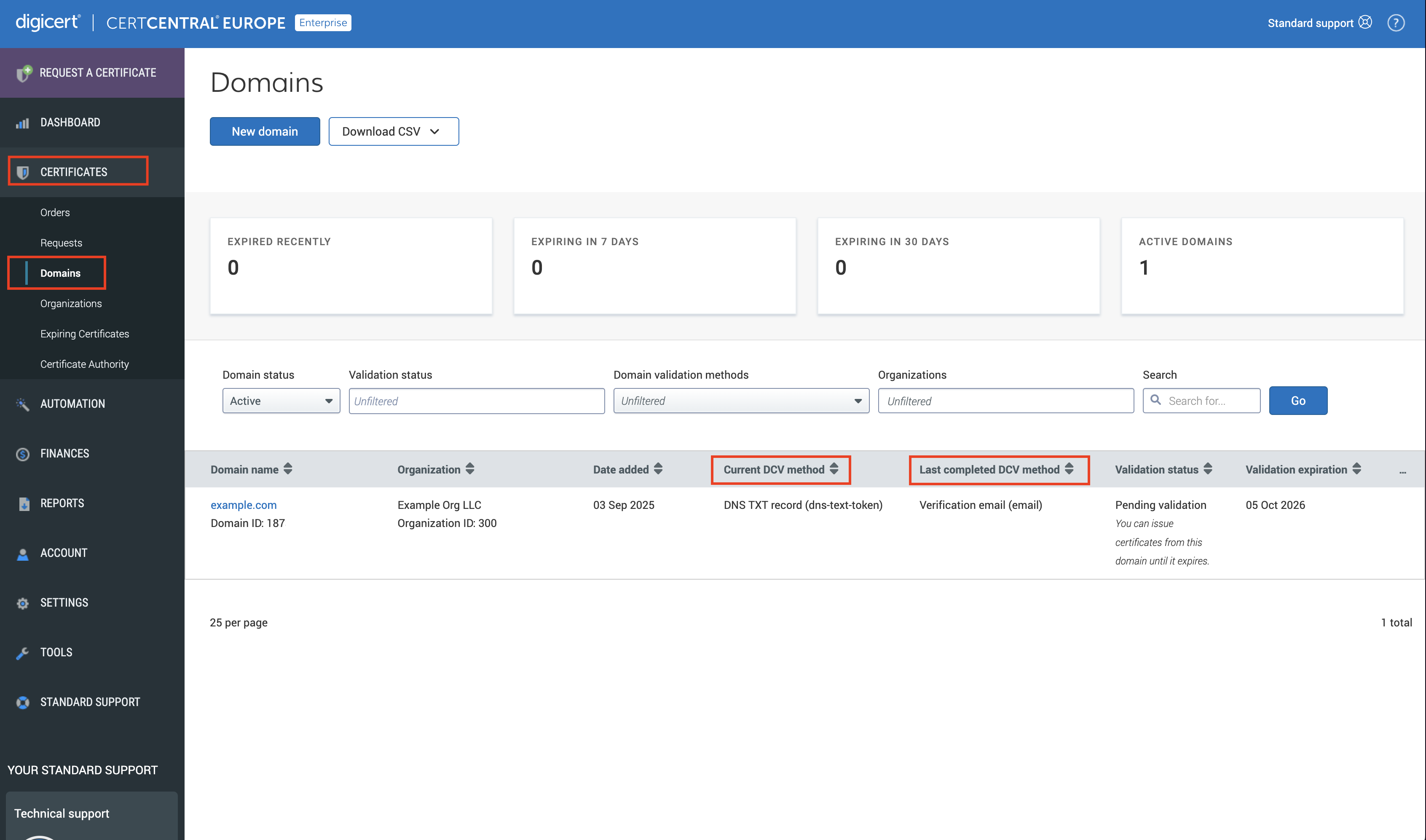
Domain details page
September 24, 2025
CertCentral: Fixed an issue where CertCentral didn't consistently enforce division-specific domain restrictions
DigiCert fixed an issue where CertCentral wasn't consistently enforcing the list of allowed domains for a division. This bug affected certificate request submitted via CertCentral and the Services API (application programming interface).
With this update, certificate requests within a division can’t include unapproved domains.
September 23, 2025
CertCentral: New product setting for all products
To make it easier to get a certificate with Linux formatting, DigiCert has introduced a new setting for all our certificates: Use Linux newlines for certificate formatting instead of Windows formatting.
By default, DigiCert uses the Windows formatting for our certificates. Previously, to get a certificate with Linux formatting, you had to convert it manually or use a program that modified the formatting for you.
With this new setting, if your certificate process requires Linux formatting, you can configure a product setting to download the certificate with Linux newline format.
See for yourself
You must be a CertCentral administrator to view and edit a product's settings.
In CertCentral, in the left menu, go to Settings > Product Settings.
On the Product Settings page, in the Product column, select a product, such as a TLS certificate.
In the Product Settings column, go to Certificate formatting for downloading a certificate. You should see the new setting, Use Linux newlines certificate formatting instead of Windows formatting.
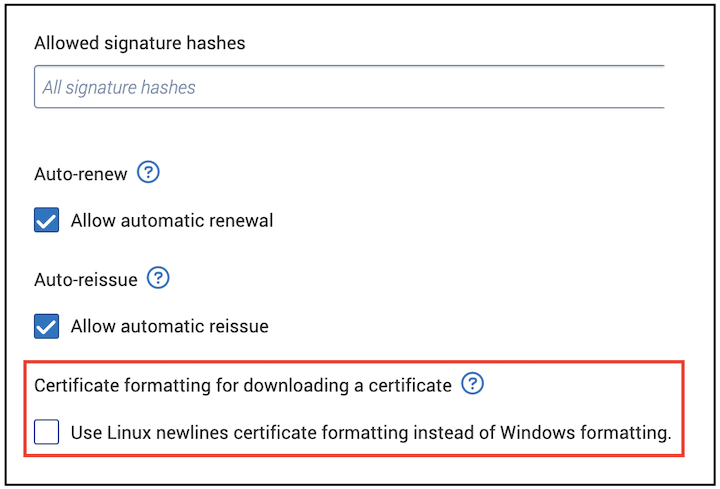
Why should I use Linux newlines formatting?
Use Linux formatting if your platform or system just supports Linux newlines, or if you’re a former QuoVadis TrustLink Enterprise customer.
September 22, 2025
Included in this update:
DigiCert adding new dedicated IPv4 addresses
On September 22, 2025, DigiCert will add a secondary CDN (content delivery network) with more dedicated IPv4 addresses for specific services.
To learn more about these IPv4 addresses and the affected services, see our knowledge base article, DigiCert Certificate Status IP Addresses.
Notice
Important update: DigiCert has postponed adding the new dedicated IPv4 addresses until September 22, 2025. We originally planned this work for September 8, 2025.
Why is DigiCert adding a secondary CDN?
We’re adding a secondary CDN to increase global resiliency and performance.
What do I need to do to prepare for the new dedicated IP addresses?
Does your company use allowlists to control outgoing traffic?
If not, no action is required. Your DigiCert services will continue to work as they did before we added the secondary CDN.
If yes, update your allowlists. Make sure they include the new IPv4 addresses before September 22, 2025, to keep your DigiCert services running as they were before we added the secondary CDN.
Affected platforms:
CertCentral®
CertCentral® Europe
DigiCert® ONE United States, Netherlands, Switzerland, and Japan instances*
QuoVadis® Trustlink
PKI Platform 8
Warning
*If Trust Lifecycle Manager, Software Trust Manager, or Content Trust Manager (United States, Switzerland, Netherlands, Australia, or Japan) uses public certificates from CertCentral, CertCentral Europe, or PKI Platform 8, you may want to add these IP addresses to your allowlist.
OCSP or CRL distribution endpoints using any of the following subdomains aren’t affected:
one.digicert.com
one.nl.digicert.com
one.ch.digicert.com
one.au.digicert.com
one.digicert.co.jp
one.oracle.digicert.com
Important HTTP protocol changes for OCSP and CRL certificate status checks
Beginning September 22, 2025, DigiCert will only support Hypertext Transfer Protocol (HTTP)/1.0 with a proper Host header, HTTP/1.1, and HTTP/1.2 connections for Online Certificate Status Protocol (OCSP) and certificate revocation lists (CRL) checks.
Notice
Important Update: DigiCert postponed only supporting HTTP/1.0 connections with a proper Host header for OCSP and CRL certificate status verification checks until September 22, 2025. We originally planned this work for September 8, 2025.
Why is DigiCert making this change?
By only supporting HTTP/1.0 with a proper Host header or HTTP/1.1 and later, DigiCert aligns with modern internet standards and removes outdated limitations, such as:
Lack of persistent (keep alive) connections
Inefficient or absent caching directives
Incomplete support for modern HTTP headers that underpin today’s security and performance best practices
What do I need to do?
Before September 22, 2025, ensure that all OCSP and CRL integrations for certificate status verification use HTTP/1.0 connections with a proper Host header or HTTP/1.1 or later versions of the protocol.
Verify every client, agent, and integration that communicates with DigiCert OCSP and CRL services uses HTTP/1.0 with a proper Host header or HTTP/1.1 or HTTP/1.2.
Update or replace any legacy software that still use HTTP/1.0 without a proper Host header for OCSP and CRL certificate status verification.
Monitor for blocked OCSP and CRL certificate status verification requests.
Failure to upgrade protocol support may interrupt workflows related to OCSP and CRL certificate status verification.
September 8, 2025
Included in this update:
DigiCert adding new dedicated IPv4 addresses
On September 8, 2025, DigiCert will add a secondary CDN (content delivery network) with more dedicated IPv4 addresses for specific services.
To learn more about these IPv4 addresses and the affected services, see our knowledge base article, DigiCert Certificate Status IP Addresses.
Warning
Important Update: DigiCert has postponed adding the new dedicated IPv4 addresses until September 22, 2025. See our September 22, 2025, entry.
Important HTTP protocol changes for OCSP and CRL certificate status checks
Beginning September 22, 2025, DigiCert will only support HTTP/1.0 connections with a proper Host header, as well as HTTP/1.1 and HTTP/1.2, for Online Certificate Status Protocol (OCSP) and certificate revocation lists (CRL) checks.
Warning
Important Update: DigiCert has postponed the move to only supporting HTTP/1.0 connections with a proper Host header for OCSP and CRL certificate status verification checks until September 22, 2025. See our September 22, 2025, entry.
September 6, 2025
Included in this update:
Upcoming scheduled Europe maintenance
DigiCert will perform scheduled maintenance on September 6, 2025, 17:00 - 19:00 CEST (15:00 - 17:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn how the September 6 maintenance affects other DigiCert services, such as the ADSS and PrimoSign signing services, see the DigiCert Europe 2025 maintenance schedule.
What can I do?
Plan accordingly:
Schedule high-priority orders, renewals, and reissues before maintenance begins or when maintenance is complete.
Expect interruptions if you use the application programming interface (API) for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts for when maintenance begins and ends.
See the DigiCert Europe 2025 maintenance schedule for maintenance dates and times
Services are restored when the maintenance is finished.
Upcoming scheduled Global maintenance
DigiCert will perform scheduled maintenance on September 6, 2025, 22:00 – 24:00 MDT (September 7, 2025, 04:00 – 06:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
What can I do?
Plan accordingly:
Schedule high-priority orders, renewals, and reissues before maintenance begins or when maintenance is complete.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts for when maintenance begins and ends.
See the DigiCert Global 2025 maintenance schedule for maintenance dates and times.
Services are restored when the maintenance is finished.
September 3, 2025
CertCentral: Improvements to the certificate request approval process
DigiCert updated the certificate request approval process in CertCentral. We no longer require administrators and managers to be “verified contacts” or “authorized representatives” for an organization to approve certain types of certificate requests.
Previously, administrators and managers needed to be “verified contacts” or “authorized representatives” for an organization. This requirement often caused delays in the certificate issuance process when:
A verified contact or authorized representative wasn’t an administrator or manager in the CertCentral account.
An administrator or manager wasn’t a verified contact or authorized representative for the organization on the certificate.
With this change, administrators and managers can now approve certificate requests—such as for extended validation (EV) TLS or PKIo Private Services Server—without needing to be verified contacts or authorized representatives. However, if the person approving the certificate request is a verified contact or authorized representative for the organization in the certificate, their approval also serves as an order approval, enabling DigiCert to process and issue the certificate.
Background
Verified contact and authorized representative
A verified contact or authorized representative is an individual who represents an organization and is authorized to approve certificate orders on behalf of the organization.
Certificate request approval
If your certificate issuance process includes an approval step, an administrator/manager must approve your certificate request before it’s submitted to DigiCert for processing. Learn how to manage your certificate request approvals.
Certificate order approval
A verified contact or authorized representative for the organization included in the certificate must approve certain certificate orders before DigiCert can issue the certificate.
September 1, 2025
DigiCert using MPIC to verify domain control and perform CAA checks
Beginning September 1, 2025, DigiCert will enhance its certificate validation process by implementing the next phase of Multi-Perspective Issuance Corroboration (MPIC) per CA/Browser Forum requirements.
With the first phase of MPIC earlier this year, DigiCert began checking domain control and CAA record details from multiple network locations.
With the next phase of MPIC beginning September 1, 2025, DigiCert will add more network perspectives (up to six more) and will enforce “corroboration.”
Corroboration means multiple network perspectives must return the same domain name system (DNS) record details or website file contents before the domain can be considered validated and the certificate can be issued.
MPIC requirements apply to both domain control validation (DCV) and Certificate Authority Authorization (CAA) checks. For more details about this change and what you need to do to prepare, read our knowledge base article.
How does the MPIC process work?
DigiCert conducts a standard domain validation and CAA record check from our primary network. We then repeat this check six times from more remote locations, each on different networks in different geographical regions.
To verify your domain control, pass the CAA checks, and issue a certificate, at least four of the six remote locations must confirm the details obtained from the primary network.
This redundancy provides stronger protection against security threats that helps catch and block unauthorized attempts to intercept or alter data as it travels across networks. For you, this means enhanced security and increased confidence that only authorized parties can obtain certificates for your domains.
What do I need to do?
To prepare for MPIC, you should have little to do before we implement this new process on September 1, 2025. However, depending on the DCV method you’re using, there may be specific tasks you must finish, while other aspects may relate more to troubleshooting.
Start by auditing your current validation setup. Verify what DCV methods you’re using. Are you using the HTTP Practical demonstration, DNS TXT record, or Email to CAA contact?
If using HTTP Practical Demonstration, check for anything that could block or delay validation requests from multiple locations, like strict network controls. See Add User Agent DigiCert DCV Bot/1.1 or IP addresses to your allowlist.
If using DNS-based DCV methods, such as DNS TXT record or Email to DNS TXT contact, check for inconsistent DNS behavior. See Verify DNS record access – troubleshooting.
Learn more:
August 12, 2025
Included in this update:
CertCentral: New extended key usage options available until May 1, 2026
From August 12, 2025, to May 1, 2026, CertCentral is providing two new extended key usage (EKU) options on the public TLS/SSL certificate request forms under Additional certificate options.
Available extended key usage (EKU) options
Server Authentication and Client Authentication
Server Authentication
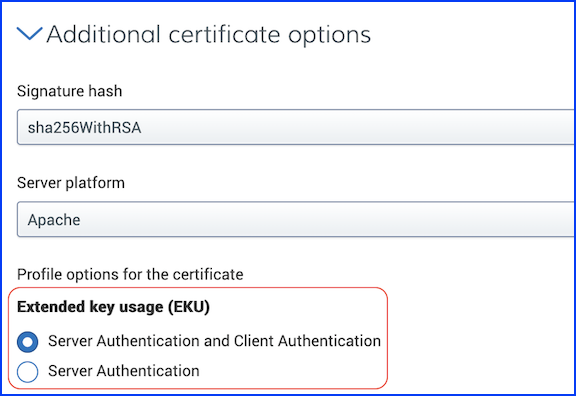
You can customize which option is selected by default from your TLS certificate’s Product Setting page in CertCentral.
Default Extended Key Usage menu options
Server Authentication and Client Authentication
Server Authentication
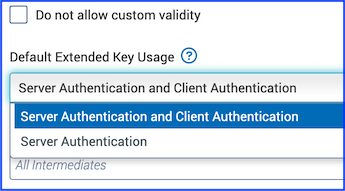
Resources
Background
Until October 1, 2025, DigiCert automatically includes both the Server Authentication and Client Authentication extended key usages (EKUs) by default in all public TLS certificates.
Beginning October 1, 2025, DigiCert will change the public TLS certificate issuance process and include just the Server Authentication EKU by default in all public TLS certificates. See the October 1, 2025, change log entry.
Beginning May 1, 2026, DigiCert will issue all public TLS certificates with just the Server Authentication EKU. We’ll remove the EKU options from CertCentral. See the May 1, 2026, change log entry.
For more information about DigiCert's timeline for phasing out the Client Authentication EKU in our public TLS certificates, read our knowledge base article about sunsetting the client authentication EKU.
CertCentral Services API
Until May 1, 2026, you can include the Server Authentication and Client Authentication EKUs in your public TLS/SSL certificates requested via the API. For more details, refer to the Certificate profile options table in the Glossary and the public TLS certificate order endpoints.
Certificate profile options
server_client_auth_ekuInclude both the Server Authentication and Client Authentication EKUs in your public Organization Validation (OV), Extended Validation (EV), and Domain Validation (DV) TLS/SSL certificates.
server_auth_only_ekuInclude the Server Authentication EKU in your public OV, EV, and DV TLS/SSL certificates.
Beginning May 1, 2026, DigiCert will no longer support these Certificate profiles for public TLS certificate requests placed through API Integrations. We’ll issue all public TLS certificates with just the Server Authentication EKU.
DigiCert: Updating the names of our Secure Email and Document Signing products
DigiCert is updating its Secure Email and Document Signing product names to provide better clarity.
Updated product name | Former product names |
|---|---|
Secure Email for Individual Mailbox | Secure Email for Individual |
Secure Email for Employee | Secure Email for Business |
Secure Email for Organization | Secure Email for Organization (no name change) |
To learn more about these products, see Secure Email products. | |
Updated product name | Former product names |
|---|---|
Document Signing for Individual | Document Signing for Individual (no name change) |
Document Signing for Employee | Document Signing for Business – Employee |
Document Signing for Organization | Document Signing for Business – Group |
To learn more about these products see Document Signing products. | |
API product identifiers
The product name change doesn’t affect the product identifiers (IDs). Continue to use these product IDs to order these certificates via the CertCentral Services API.
Updated product name | Product IDs |
|---|---|
Secure Email for Individual Mailbox |
|
Secure Email for Employee |
|
Secure Email for Organization |
|
Document Signing for Individual |
|
Document Signing for Employee |
|
Document Signing for Organization |
|
See the Product identifiers table in the Glossary of our Services API developer documentation. | |
CertCentral Services API: Fixed a bug where the organization ID wasn’t always returned in the response
DigiCert fixed a bug in the Orders endpoints where the organization ID wasn’t always included in the response if creating a new organization as part of the order. This bug affected the order endpoints that include an organization in the request, such as Order Basic OV and Order code signing certificate. The bug didn’t affect endpoints that don’t include an organization in the request, such as Order GeoTrust DV SSL.
Now, if you create a new organization as part of your certificate request, the new organization’s ID is always included in the response.
August 9, 2025
Included in this update:
Upcoming scheduled Europe maintenance
DigiCert will perform scheduled maintenance on August 9, 2025, 17:00 - 19:00 CEST (15:00 - 17:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn about the impact of the August 9 maintenance on other DigiCert services, such as the ADSS and SealSign signing services, see the Saturday, August 9 entry in the DigiCert Europe 2025 maintenance schedule.
What can I do?
Plan accordingly:
Schedule high-priority orders, renewals, and reissues before maintenance begins or once maintenance is complete.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts for once maintenance begins and ends.
See the DigiCert Europe 2025 maintenance schedule for maintenance dates and times.
Services are restored once the maintenance is finished.
Upcoming scheduled global maintenance
DigiCert will perform scheduled maintenance on August 9, 2025, 22:00 – 24:00 MDT (August 10, 2025, 04:00 – 06:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn about the impact of the August 9 maintenance on other DigiCert services, such as Document Trust Manager, see the Saturday, August 9 entry in the DigiCert Global 2025 maintenance schedule.
What can I do?
Plan accordingly:
Schedule high-priority orders, renewals, and reissues before maintenance begins or once maintenance is complete.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts for once maintenance begins and ends.
See the DigiCert Global 2025 maintenance schedule for maintenance dates and times.
Services are restored once the maintenance is finished.
July 23, 2025
Part 1: Truncating certificate validity as DigiCert transitions to dedicated TLS root hierarchies
Beginning July 23, 2025, DigiCert automatically truncates the validity of certificates issued from the intermediate CA (ICA) certificates in the table below. All affected certificates are set to expire no later than May 14, 2026. This expiration date ensures these certificates expire before the scheduled revocation date of May 15, 2026. See the May 15, 2026, change log entry.
Products with validity truncated to May 14, 2026 | Issuing intermediate CA |
|---|---|
Public TLS certificates | DigiCert Global CA G2 |
Public S/MIME certificates | DigiCert G2 SMIME RSA4096 SHA384 2024 CA1 |
Public code signing certificates | DigiCert Global G3 Code Signing ECC SHA384 2021 CA1 |
Public code signing certificates | DigiCert Global G3 Code Signing ECC P256 SHA384 2021 CA1 |
Public code signing certificates | DigiCert Global G3 Code Signing Europe ECC P-384 SHA384 2023 CA1 |
What if I don't want certificates with a truncated validity?
To get certificates that expire after May 14, 2026, use the replacement/new intermediate certificate to issue your certificates. To find your certificate’s replacement ICA certificate, see the Intermediate CA certificate and their associated end-entity certificates to be revoked on May 15, 2026 table in our knowledge base article.
Why is DigiCert moving to dedicated TLS root hierarchies
The Google Chrome Root Program requires Certificate Authorities (CAs) to use dedicated TLS root hierarchies for issuing public TLS certificates.
To enhance digital trust and comply with the evolving requirements of browser root programs, DigiCert is transitioning to single-purpose root hierarchies dedicated to issuing public TLS end-entity certificates.
Additional information
July 12, 2025
Included in this update:
Upcoming scheduled Europe maintenance
DigiCert will perform scheduled maintenance on July 12, 2025, 17:00 - 19:00 CEST (15:00 - 17:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn how the July 12 maintenance effects the Legacy QuoVadis PrimoSign signing service, see the Saturday, July 12 entry in the DigiCert Europe 2025 maintenance schedule.
What can I do?
Plan accordingly:
Schedule high-priority orders, renewals, and reissues before or after the maintenance window.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts for once maintenance begins and ends.
See the DigiCert Europe 2025 maintenance schedule for maintenance dates and times.
Services will be restored once the maintenance is finished.
Upcoming scheduled Global maintenance
DigiCert will perform scheduled maintenance on July 12, 2025, 22:00 – 24:00 MDT (July 13, 2025, 04:00 – 06:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn how the July 12 maintenance effects the DigiCert ONE United States location, see the Saturday, July 12 entry in the DigiCert Global 2025 maintenance schedule.
What can I do?
Plan accordingly:
Schedule high-priority orders, renewals, and reissues before or after the maintenance window.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts for once maintenance begins and ends.
See the DigiCert Global 2025 maintenance schedule for maintenance dates and times.
Services will be restored once the maintenance is finished.
July 10, 2025
Industry changes affecting S/MIME certificates: Sunsetting the Legacy generation profile
On July 10, 2025, at 11:00 MDT (17:00 UTC), DigiCert will no longer accept S/MIME certificate requests using the Legacy certificate profile. All new S/MIME certificate requests must use the Strict or Multipurpose certificate profile (the S/MIME baseline requirements refer to these as Generation profiles). This change affects new, renewed, and reissued certificate requests. To learn more about this change, see our knowledge base article, New Certificate Profile Requirements for Public Secure Email (S/MIME) Certificates 2025.
Important
Update: DigiCert postponed the acceptance date for S/MIME certificate requests using the Legacy certificate profile until July 10, 2025. We originally planned this work for July 1, 2025.
How does the new certificate profile requirement affect my public S/MIME certificates?
Existing S/MIME certificates using the Legacy certificate profile
Your existing S/MIME certificates issued with the Legacy certificate profile are not affected by the new certificate profile requirement. You can continue to use these certificates until they expire.
However, starting July 10, 2025, if you reissue or when you renew S/MIME certificates with the Legacy profile, you must use the Strict or Multipurpose profile instead.
New S/MIME certificate requests starting July 10, 2025
On July 10, 2025, we will change the default certificate profile from Legacy to either Strict or Multipurpose. See the Profile mappings table below.
Product | Certificate profiles before July 10, 2025 | Certificate profiles starting July 10, 2025 |
|---|---|---|
|
|
|
| Legacy | Multipurpose |
*In CertCentral, on the Product Settings page, administrators can change the default certificate profile to Multipurpose, if needed. | ||
What can I do?
Order S/MIME certificates with the Legacy certificate profile before July 10, 2025.
To get a sponsor-validate S/MIME certificate, such as a Secure Email for Business, with the recipient’s email address as the common name without the subject individual’s first and last name or pseudonym, you must order your S/MIME certificates with the Legacy certificate profile before July 10, 2025.
See the Certificate profile comparison table, in our knowledge base article, New Certificate Profile Requirements for Public Secure Email (S/MIME) Certificates 2025.
Prepare your S/MIME certificate process to align with the new certificate profile requirement.
Ultimately, the most important thing you can do is update your S/MIME certificate issuance to make sure it aligns with the new requirement and continues to work the way it did before July 10, 2025.
See the sections listed below, in our knowledge base article:
S/MIME certificates: End of issuance for certificate using the Legacy certificate profile
On July 10, 2025, at 11:00 MDT (17:00 UTC), DigiCert will no longer issue S/MIME certificates using the Legacy certificate profile. To learn more about this change, see our knowledge base article, New Certificate Profile Requirements for Public Secure Email (S/MIME) Certificates 2025.
Notice
Update: DigiCert postponed the end of issuance for S/MIME certificates using the Legacy certificate profile until July 10, 2025. We originally planned this work for July 8, 2025.
How does this affect me?
DigiCert will never issue your pending S/MIME certificate with the Legacy certificate profile. If you no longer need the certificate, cancel the pending order.
If you still need the S/MIME certificate, cancel the pending order and then do the following as needed:
Secure Email Certificates
To get your Secure Email for Individual, Secure Email for Business, or Secure Email for Organization certificate, place a new order using the Strict or Multipurpose certificate profile instead.
CertCentral: Secure Email Certificates
CertCentral Services API: Order Secure Email (S/MIME) certificate
Old S/MIME certificates
In CertCentral, you can no longer order Premium, Email Security Plus, Digital Signature Plus, and Class 1 S/MIME certificates. You must request a Secure Email Certificate instead.
Our new Secure Email for Individual certificate replaces the Class 1 S/MIME certificate.
Our new Secure Email for Business certificate replaces the Premium, Email Security Plus, and Digital Signature Plus certificates.
If using the CertCentral Services API, you can still order Premium, Email Security Plus, Digital Signature Plus, and Class 1 S/MIME certificates until we deprecate them in early 2026. We will use the Multipurpose certificate profile to issue these certificates. See Order client certificate.
July 8, 2025
End of life for reusing existing WHOIS-based domain validations
On July 8, 2025, DigiCert will stop reusing existing WHOIS-based domain validations, regardless of whether previously obtained information is within the allowed 397-day reuse period and regardless of the WHOIS method.
These changes affect all web-based WHOIS domain validations, including the following certificate types: TLS, Verified Mark and Common Mark, Secure Email (S/MIME), DirectAssured, and DirectTrust. See End of life for WHOIS-based DCV methods.
How does this affect me?
Have you used WHOIS-based Email or Phone DCV methods to validate your domains? Then you will need to revalidate your domains the next time you want to get a certificate.
Important
End of life for reusing existing WHOIS-based domain validations does not affect your existing certificates. Your certificates will remain valid and trusted until they expire.
What do I need to do?
Do you rely on immediate certificate issuance?
If not, then no action is required until the next time you order a certificate.
The next time you order a certificate, you must choose a non-WHOIS-reliant domain control validation (DCV) method, such as DNS Text Record. To continue validating domains via email, set up a DNS TXT Email Contact or a Constructed Email address.
If yes, then action is required to avoid potential disruption to your certificate issuance.
For those that rely on instant issuance of certificates, you must revalidate your domains using a non-WHOIS-reliant DCV method , such as DNS Text Record, or to continue validating domains via email, set up a DNS TXT Email Contact or a Constructed Email address before July 8.
Why will DigiCert stop reusing existing WHOIS-based domain validations?
The industry recently adopted Ballot SC-80v3: Sunset the Use of WHOIS to Identify Domain Contacts and Relying DCV Methods. To comply with industry changes mandated by the ballot, certificate authorities (CAs), such as DigiCert, must stop using WHOIS to identify domain contacts for email, fax, SMS, postal mail, and phone domain control validation (DCV) methods. Note that DigiCert only supports the email and phone WHOIS-based DCV methods.
References
Industry changes to S/MIME certificates: Sunsetting the Legacy generation profile
On July 8, 2025, at 11:00 MDT (17:00 UTC), DigiCert will no longer accept S/MIME certificate requests using the Legacy certificate profile. All new S/MIME certificate requests must use the Strict or Multipurpose certificate profile (the S/MIME baseline requirements refer to these as Generation profiles).
Notice
Update: DigiCert postponed the acceptance date for S/MIME certificate requests using the Legacy certificate profile until July 10, 2025. See our July 10, 2025, entry.
S/MIME certificates: End of issuance for certificate using the Legacy certificate profile
On July 8, 2025, at 11:00 MDT (17:00 UTC), DigiCert will no longer issue S/MIME certificates using the Legacy certificate profile.
Notice
Update: DigiCert postponed the end of issuance for S/MIME certificates using the Legacy certificate profile until July 10, 2025. See our July 10, 2025, entry.
July 1, 2025
Industry changes to S/MIME certificates: Sunsetting the Legacy generation profile
On July 1, 2025, at 11:00 MDT (17:00 UTC), DigiCert will no longer accept S/MIME certificate requests using the Legacy certificate profile. All new S/MIME certificate requests must use the Strict or Multipurpose certificate profile (the S/MIME baseline requirements refer to these as Generation profiles).
Notice
Update: DigiCert postponed the acceptance date for S/MIME certificate requests using the Legacy certificate profile until July 8, 2025. See our July 8, 2025, entry.
June 19, 2025
General availability of DigiCert’s X9 PKI for TLS product
DigiCert is excited to announce the release of its new X9 PKI for TLS product. The X9 PKI for TLS certificate is perfect for organizations that depend on TLS certificates for secure host-to-host communications, including mutual TLS (mTLS), APIs, and other non-web browser use cases.
Please contact your account representative or DigiCert Support today, to enable the X9 PKI for TLS product in your CertCentral account.
How the X9 PKI for TLS certificate came to be
Regulated by the ASC X9 standards body, DigiCert's X9 PKI for TLS certificate is governed by an independent certificate policy that is not affiliated with any browsers while ensuring interoperability through a common root of trust.
Your X9 PKI for TLS certificate supports client and server authentication Extended Key Usage (EKUs), addressing today's unique demands for control, security, flexibility, and scalability with encryption, identity verification, and cross-certification. Learn more about X9 PKI and schedule a consultation.
CertCentral resources
CertCentral Services API resources
June 7, 2025
Included in this update:
Upcoming scheduled Europe maintenance
DigiCert will perform scheduled maintenance on June 7, 2025, 17:00 - 19:00 CEST (15:00 - 17:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn more about the impact of the June 7 maintenance on other DigiCert services, such as the ADSS and PrimoSign signing services, see the Saturday, June 7 entry in the DigiCert Europe 2025 maintenance schedule.
What can I do?
Plan accordingly:
Schedule high-priority orders, renewals, and reissues before or after the maintenance window.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts for when maintenance starts and ends.
See the DigiCert Europe 2025 maintenance schedule for maintenance dates and times.
Service will be restored as soon as maintenance is completed.
Upcoming scheduled Global maintenance
DigiCert will perform scheduled maintenance on June 7, 22:00 – 24:00 MDT (June 8, 04:00 – 06:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn more about the impact of the June 7 maintenance on other DigiCert services, such as Document Trust Manager and the PrimoSign signing service, see the Saturday, June 7 entry in the DigiCert Global 2025 maintenance schedule.
What can I do?
Plan accordingly:
Schedule high-priority orders, renewals, and reissues before or after the maintenance window.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts for when maintenance starts and ends.
See the DigiCert Global 2025 maintenance schedule for maintenance dates and times.
Services will be restored as soon as the maintenance is completed.
June 3, 2025
CertCentral: Added the ability to download a revoked certificate
In CertCentral, we added the ability to download a revoked certificate. From the certificate's Order # details page, you can now download a revoked certificate. In the CertCentral Services API, you can now use the existing download certificate endpoints to download a revoked certificate. More details below.
CertCentral
Before, the Download certificate option only appeared for issued and expired certificates. Now, if needed, you can download a revoked certificate on the certificate's Order # details page or its Certificate history tab.
Download certificate documentation:
CertCentral Services API
In the Services API, we updated the download certificate endpoints, allowing you to download a revoked certificate. Previously, the API returned an error message when attempting to download a revoked certificate. Now, if needed, use any download certificate endpoint to get a copy of a revoked certificate (for example, a revoked TLS certificate).
API download certificate endpoints:
May 10, 2025
Included in this update:
Upcoming scheduled Europe maintenance
DigiCert will perform scheduled maintenance on May 10, 2025, 17:00 - 19:00 CEST (15:00 - 17:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn more about the impact of the May 10 maintenance on other DigiCert services, such as the PrimoSign signing service, see the Saturday, May 10 entry in the DigiCert Europe 2025 maintenance schedule.
What can I do?
Plan accordingly:
Schedule high-priority orders, renewals, and reissues before or after the maintenance window.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts for when maintenance starts and ends.
See the DigiCert Europe 2025 maintenance schedule for maintenance dates and times.
Services will be restored as soon as the maintenance is completed.
Upcoming scheduled Global maintenance
DigiCert will perform scheduled maintenance on May 10, 2025, 22:00 – 24:00 MDT (May 11, 2025, 04:00 – 06:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn more about the impact of the May 10 maintenance on other DigiCert services, such as the Trust Lifecycle Manager and DigiCert ONE, see the Saturday, May 10 entry in the DigiCert Global 2025 maintenance schedule.
What can I do?
Plan accordingly:
Schedule high-priority orders, renewals, and reissues before or after the maintenance window.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts for when maintenance starts and ends.
See the DigiCert Global 2025 maintenance schedule for maintenance dates and times.
Services will be restored as soon as the maintenance is completed.
May 8, 2025
End of life for new WHOIS-based domain validations, regardless of WHOIS lookup method
On May 8, 2025, DigiCert will no longer support WHOIS-based DCV email and phone methods. DigiCert systems will stop querying WHOIS entirely for domain validations.
These changes affect all web-based WHOIS domain validations, including the following certificate types: TLS, Verified Mark and Common Mark, Secure Email (S/MIME), DirectAssured, and DirectTrust. See End of life for WHOIS-based DCV methods.
How does this affect me?
Are you using WHOIS-based Email or Phone DCV methods?
Then, the next time you validate your domains, you must use a different DCV method, such as DNS Text Record. If you want to continue to use DCV email, set up a DNS TXT Email Contact or a Constructed Email address.
Important
The end of life for WHOIS-based DCV methods does not affect your existing certificates. Your certificates will remain valid and trusted until they expire.
Why will DigiCert end support for new WHOIS-based domain validations?
The industry recently adopted Ballot SC-80v3: Sunset the Use of WHOIS to Identify Domain Contacts and Relying DCV Methods. To comply with industry changes mandated by the ballot, certificate authorities (CAs), such as DigiCert, must stop using WHOIS to identify domain contacts for email, fax, SMS, postal mail, and phone domain control validation (DCV) methods. Note that DigiCert only supports the email and phone WHOIS-based DCV methods.
References
April 12, 2025
Included in this update:
Upcoming scheduled Europe maintenance
DigiCert will perform scheduled maintenance on April 12, 2025, 17:00 - 19:00 CEST (15:00 - 17:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn more about the impact of the April 12 maintenance on other DigiCert services, such as the ADSS and PrimoSign signing services, see the Saturday, April 12 entry in the DigiCert Europe 2025 maintenance schedule.
What can I do?
Plan accordingly:
Schedule high-priority orders, renewals, and reissues before or after the maintenance window.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts for when maintenance starts and ends.
See the DigiCert Europe 2025 maintenance schedule for maintenance dates and times.
Services will be restored as soon as the maintenance is completed.
Upcoming scheduled Global maintenance
DigiCert will perform scheduled maintenance on April 12, 2025, 22:00 – 24:00 MDT (April 13, 2025, 04:00 – 06:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
We canceled the maintenance, which was to affect other DigiCert services. To learn more, see the Saturday, April 12 entry in the DigiCert Global 2025 maintenance schedule.
What can I do?
Plan accordingly:
Schedule high-priority orders, renewals, and reissues before or after the maintenance window.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts for when maintenance starts and ends.
See the DigiCert Global 2025 maintenance schedule for maintenance dates and times.
Services will be restored as soon as the maintenance is completed.
March 19, 2025
DigiCert document signing certificates for individuals, employees, and organizations
We are happy to announce the release of our new Document Signing products. Starting March 19, DigiCert will offer three new Document Signing certificates to apply electronic signatures or seals:
Document Signing for Individual
Document Signing for Business – Employee
Document Signing for Business – Group
Your electronic signature or seal certifies the document's origin, authenticity, and integrity, assuring the recipient that the document is from you and has not been altered.
Our new Document Signing certificates:
Are compatible with Adobe Acrobat, DocuSign, Microsoft Office, OpenOffice, and LibreOffice documents.
Include the following private key and certificate storage options, referred to as key provisioning methods:
DigiCert-supplied hardware token
Your own DigiCert-supported FIPS 140-2 Level 2 hardware token
Your FIPS 140-2 Level 2 hardware security module (HSM)
Learn more about DigiCert’s new document signing products, Document Signing products.
CertCentral: End of life for legacy Document Signing products
DigiCert is deprecating our older Document Signing products: Document Signing - Individual (500/2000) and Document Signing – Organization (2000/5000) certificates.
On March 19, we replaced the legacy document signing products in CertCentral with the new ones. When you renew or reissue a legacy document signing certificate, we will redirect you to its replacement certificate.
Legacy certificate replacements
Document Signing for Individual certificate replaces the Document Signing - Individual (500/2000) certificate.
Document Signing for Business – Employee certificate replaces the Document Signing - Organization (2000/5000) certificate, where the subject individual is the common name.
Document Signing for Business – Group certificate replaces the Document Signing - Organization (2000/5000) certificate, where the organization is the common name.
To learn more about the new certificates,visit the Document Signing products page.
How will the renewal and reissue processes work?
Reissues
When reissuing your older document signing certificate, we will redirect you to request one of the new certificates instead. The new certificate will have the same validity as your existing certificate. Just like a reissue, the new certificate will be free.
Renewals
When renewing your older document signing certificate, we will redirect you to request one of the new certificates instead.
To learn more about the legacy certificate replacements, see the Legacy DigiCert Document Signing products section on the Document Signing products page.
March 13, 2025
DigiCert to start checking CAA resource records before issuing Secure Email (S/MIME) certificates
Starting March 13, 2025, at 10:00 MDT (16:00 UTC), before DigiCert issues your Secure Email (S/MIME) certificates, we must check, process, and abide by your email domains’ DNS Certification Authority Authorization (CAA) resource records. To learn more about why we are making this change, see Why DigiCert will check CAA Resource Records before issuing Secure Email (S/MIME) certificates below.
How does the CAA record check work?
Before issuing a Secure Email (S/MIME) certificate with email domains, such as john.doe@example.com, DigiCert must check each email domain’s CAA record to verify that we are authorized to issue that certificate. DigiCert can only issue the Secure Email (S/MIME) certificate if one of the following conditions is met:
We do not find a CAA record for your email domain.
We find a CAA record for your email domain authorizing DigiCert to issue your S/MIME certificate.
For example:
yourdomain CAA 0 issuemail "digicert.com"We only find CAA records for your domain without the "
issuemail" property tag.
What certificates are affected by the new CAA resource record checking requirement?
These changes affect mailbox-validated, organization-validated, and sponsor-validated Secure Email (S/MIME) certificates issued from CertCentral, Trust Lifecycle Manager, and PKI Platform 8*.
CertCentral Secure Email (S/MIME) certificates:
Secure Email for Individual
Secure Email for Organization
Secure Email for Business
Premium
Email Security Plus
Digital Signature Plus
Class 1 S/MIME
*Note: On March 14, 2025, at 23:59 UTC, DigiCert will stop issuing public S/MIME (Secure Email) certificates from DigiCert® PKI Platform 8. See Transitioning public S/MIME certificate issuance from PKI Platform 8 to Trust Lifecycle Manager in DigiCert ONE.
How does this affect me, and what must I do?
Do you have or are you planning to create DNS CAA records for your email domains?
No, I do not have or plan to create DNS CAA records for my email domains.
You are not affected by this change and there is nothing you need to do. You shouldn't notice any difference in your Secure Email (S/MIME) certificate issuance process, as having a CAA record is NOT REQUIRED for DigiCert to issue your Secure Email (S/MIME) certificate.
Yes, I have or plan to create DNS CAA records for my email domains.
You may be affected by this change. Before March 13, 2025, DigiCert recommends checking your email domains' existing DNS CAA recourse records to verify that DigiCert can issue Secure Email (S/MIME) certificates for your email domains. See How does the CAA resource record check work above.
Why DigiCert will check CAA resource records before issuing Secure Email (S/MIME) certificates
Per the Latest S/MIME Baseline Requirements, on March 15, 2025, at 00:00 UTC, all Certificate Authorities (CAs), such as DigiCert, must retrieve and process CAA records prior to issuing a certificate that includes a Mailbox Address. This new requirement allows organizations to specify which CAs are authorized to issue S/MIME certificates for mailboxes (email domains).
Remember, the CAA record check is already part of the TLS certificate issuance process. CAA records are a powerful tool for reducing the risk of nonauthorized or unknown CAs issuing certificates for your domains and mailboxes (email domains).
References
March 5, 2025
CertCentral: Modernizing your pending TLS certificate's "Need to Do" checklists
We are happy to announce that we are working on a new command center to track and complete the domain and organization validation tasks for your pending TLS certificate order.
What’s changed?
The new, interactive design for the "Need to Do" domain and organization validation checklists allows you to quickly sort and filter pending and completed tasks, making it easier to complete the validation tasks for your pending certificate order. Additionally, we included more information about the organization tasks, making it easier to understand what DigiCert needs to do and how you can help.
Try it out today. Then, let us know what you think by completing the survey in CertCentral. Your feedback is vital as we continue to develop the new validation experience.
Check it out
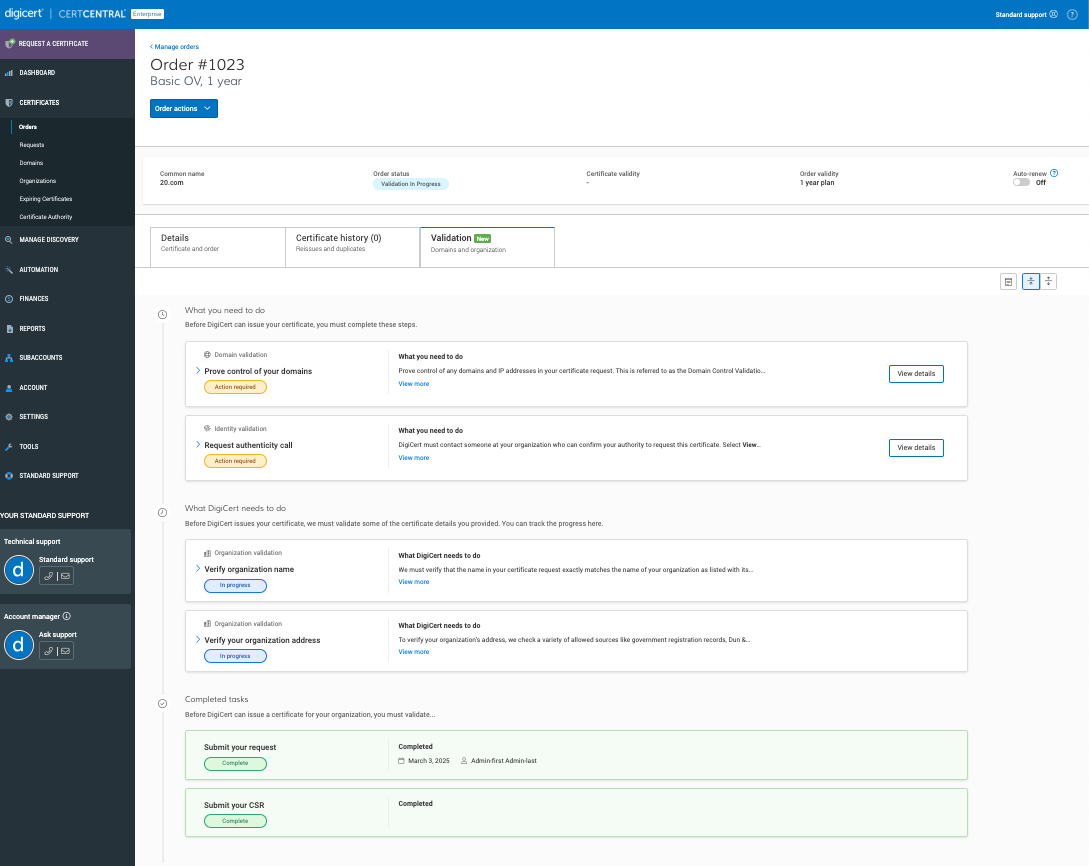
March 1, 2025
Upcoming scheduled Europe maintenance
DigiCert will perform scheduled maintenance on March 1, 2025, 17:00 - 19:00 CET (16:00 - 18:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
Other DigiCert services
To learn more about the impact of the March 1 maintenance on other DigiCert services, such as DigiCert® Content Trust Manager, see the Saturday, March 1 entry in the DigiCert Europe 2025 maintenance schedule.
What can I do?
Schedule high-priority orders, renewals, and reissues before or after the maintenance window.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts for when maintenance starts and ends.
See the DigiCert Europe 2025 maintenance schedule maintenance schedule for maintenance dates and times.
Services will be restored as soon as the maintenance is completed.
Upcoming scheduled Global maintenance
DigiCert will perform scheduled maintenance on March 1, 2025, 22:00 – 24:00 MST (March 2, 2025, 05:00 – 07:00 UTC).
How does this affect me?
Although we have redundancies to protect your services, some DigiCert services may be unavailable during this time.
What can I do?
Plan accordingly:
Schedule high-priority orders, renewals, and reissues before or after the maintenance window.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts for when maintenance starts and ends.
See the DigiCert Global 2025 maintenance schedule for maintenance dates and times.
Services will be restored as soon as the maintenance is completed.
February 15, 2025
Critical ADSS signing service upgrade in our Document Trust Manager Netherlands location
DigiCert must perform a critical upgrade on the ADSS signing service on February 15, 2025, 02:00 to 06:00 CET (01:00 – 05:00 UTC). During this time, the ADSS signing service in our DigiCert® Document Trust Manager Netherlands location will be down for approximately four hours.
How does this affect me?
The ADSS signing service upgrade starts at 02:00 CET (01:00 UTC). From 02:00 to 06:00 CET (01:00 – 05:00 UTC), the ADSS signing services will be down for approximately four hours.
Affected services
Document Trust Manager's ADSS signing service in the DigiCert® ONE Netherlands location
What can I do?
Plan accordingly:
Schedule high-priority document signings before or after the maintenance window.
Expect interruptions if you use the APIs for automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts for when maintenance starts and ends.
See the DigiCert Europe 2025 maintenance schedule for maintenance dates and times.
Services will be restored as soon as the maintenance is completed.
February 13, 2025
DigiCert to replace QuoVadis timestamping certificate
On February 13, 2025, at 23:30 MST (February 14, at 06:30 UTC), DigiCert will replace the QuoVadis timestamping certificate. Additionally, we will issue the timestamping certificate from a different intermediate CA (ICA) certificate.
New timestamping and issuing ICA certificates
tsaeursa1.digicert.eu
DigiCert QuoVadis G3 TS Europe RSA4096 SHA256 2023 CA1
Old timestamping certificate and issuing ICA certificate
eutsa01.quovadisglobal.com
eutsa01.quovadisglobal.com
Important
Update: DigiCert postponed the QuoVadis timestamping certificate replacement until February 13, 2025. We originally planned this work for February 6, 2025.
How does this affect me?
Please check your current timestamp usage for dependencies on the timestamp certificate and its issuing ICA certificate.
Does this affect my existing signatures?
No. Rolling out a new timestamping certificate does not affect your existing signatures. Timestamped signatures will remain valid, secure, and trusted.
References
February 12, 2025
DigiCert to replace QuoVadis timestamping certificate
On February 12, 2025, at 23:30 MST (February 13, at 06:30 UTC), DigiCert will replace the QuoVadis timestamping certificate. Additionally, we will issue the timestamping certificate from a different intermediate CA (ICA) certificate.
Important
Update: DigiCert has postponed the QuoVadis timestamping certificate replacement until February 13, 2025. See our February 13, 2025, change log entry.
February 11, 2025
CertCentral: Removed Mark details from the Verified Mark and Common Mark Certificate request forms and Order details pages
DigiCert removed the Mark details section from the Verified Mark and Common Mark Certificate request forms and these certificates’ pending Order details pages.
Important
This change is retroactive and removes the Mark details section from your existing pending Verified Mark and Common Mark Certificate orders.
Why did DigiCert remove the Mark details section?
With Verified Mark Certificates, too often, the requestor selected "did not know" or provided incorrect trademark or government mark information, slowing down the logo validation process instead of speeding it up.
With Common Mark Certificates, the Mark details section did not apply to Common Mark Certificates as this certificate does not require a trademarked or government mark logo.
Logo verification
DigiCert must still verify your logo before we can issue your Mark Certificate.
For Verified Mark Certificates, DigiCert must confirm your trademark is legally registered or confirm the government entity's legislation proving the mark's legitimacy.
For Common Mark Certificates, DigiCert must confirm your logo has been used for at least a year or is like your registered trademark.
References
February 6, 2025
DigiCert to replace QuoVadis timestamping certificate
On February 6, 2025, at 23:30 MST (February 7, at 06:30 UTC), DigiCert will replace the QuoVadis timestamping certificate. Additionally, we will issue the timestamping certificate from a different intermediate CA (ICA) certificate.
Important
Update: DigiCert has postponed the QuoVadis timestamping certificate replacement until February 13, 2025. See our February 13, 2025, change log entry.
February 5, 2025
CertCentral: New profile options for Secure Email certificates
Now, when you order a Secure Email for Individual, Business, or Organization certificate, you will see a Profile options menu with three profiles to choose from: Strict, Multipurpose, and Legacy.
The selected profile affects the certificate validity and the supported certificate usages. The profile may also affect what recipient information you must and can include in the certificate:
Maximum certificate validity:
825 days – Strict and Multipurpose
1185 days - Legacy
Additional certificate usages:
Non-repudiation – Strict, Multipurpose, and Legacy
Data encipherment – Multipurpose and Legacy
Client authentication – Multipurpose and Legacy
Recipient information – Secure Email for Business certificates only
You must include the recipient's first and last name or their pseudonym in the subject of the certificate.
Why does DigiCert offer three profiles?
The S/MIME Baseline Requirements currently support three profiles for Secure Email (S/MIME) certificates: Strict, Multipurpose, and Legacy.
DigiCert still supports the Legacy profile for various backward compatibility use cases, including client authentication and/or document signing. If you only use the Legacy profile because you require the additional certificate usages, we recommend moving to the newer Multipurpose profile.
Learn more
For more information about ordering your Secure Email certificate:
CertCentral: Secure Email Certificates
CertCentral Services API: Order Secure Email (S/MIME) certificate
February 1, 2025
Upcoming scheduled Europe maintenance
The ADSS signing service, PrimoSign signing service, and legacy QuoVadis certificate issuance will be down during scheduled Europe maintenance on February 1, 2025, 17:00 - 19:00 CET (16:00 - 18:00 UTC).
How does this affect me?
Document Trust Manager’s ADSS signing service maintenance – 10-minute downtime
The Document Trust Manager’s ADSS signing service maintenance in our Netherlands and Switzerland locations starts at 17:00 CET (UTC 16:00). At this time, the ADSS signing service in these locations will be down for approximately 10 minutes.
Legacy QuoVadis ADSS signing service maintenance – 10-minute downtime
The Legacy QuoVadis ADSS signing service maintenance in our Netherlands and Switzerland locations starts at 17:00 CET (UTC 16:00). At this time, the ADSS signing service in these locations will be down for approximately 10 minutes.
Legacy QuoVadis PrimoSign signing service maintenance – 60-minute downtime
The Legacy QuoVadis PrimoSign signing service maintenance starts at 17:00 CET (UTC 16:00). At this time, this PrimoSign signing service will be down for approximately 60 minutes.
Legacy QuoVadis certificate issuance – 30-minute downtime
The QuoVadis database maintenance starts at 17:00 CET (UTC 16:00). At this time, legacy QuoVadis certificate issuance will be down for up to 30 minutes.
Affected services:
Document Trust Manager’s ADSS signing service in the following locations:
DigiCert® ONE Netherlands
DigiCert® ONE Switzerland
Legacy QuoVadis services:
ADSS signing in our Netherlands and Switzerland locations
PrimoSign signing
Certificate issuance
What can I do?
Plan accordingly:
Schedule high-priority ADSS and PrimoSign document signings before or after the maintenance window.
Schedule high-priority orders, renewals, and reissues before or after the maintenance window.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts for when maintenance starts and ends.
See the DigiCert Europe 2025 maintenance schedule for maintenance dates and times.
Services will be restored as soon as the maintenance is completed.
Upcoming scheduled Global maintenance
DigiCert® PKI Platform 8 will experience brief and periodic maintenance-related service interruptions during scheduled maintenance on February 1, 2025, 22:00 – 24:00 MST (February 2, 05:00 – 07:00 UTC).
How does this affect me?
The PKI Platform 8 maintenance starts at 22:00 MST (05:00 UTC). From 22:00 to 24:00 MST (05:00 to 07:00 UTC), PKI Platform 8 will experience brief and periodic service interruptions.
Affected services
PKI Platform 8
API notes
APIs may return "503 services unavailable" errors.
Requests placed during this window that receive a "503 services unavailable" error message must be placed again after services are restored.
What can I do?
Plan accordingly:
Schedule high-priority tasks before or after the maintenance window.
Schedule high-priority orders, renewals, and reissues before or after the maintenance window.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts for when maintenance starts and ends.
See the DigiCert Global 2025 maintenance schedule for maintenance dates and times.
Services will be restored as soon as the maintenance is completed.
January 11, 2025
Upcoming scheduled Europe maintenance
The ADSS signing service, PrimoSign signing service, and some QuoVadis services will be down during scheduled Europe maintenance on January 11, 2025, 17:00 - 19:00 CET (16:00 - 18:00 UTC).
Important
We previously communicated that the ADSS signing service in our Document Trust Manager Netherlands location would be down for four hours during scheduled maintenance on January 11, 2025. However, we will now do the ADSS signing service upgrade on February 15, 2025. See the February 15, 2025 change log entry.
How does this affect me?
ADSS signing service patching (Switzerland) – 10-minute downtime
The ADSS signing service patching starts at 17:00 CET (UTC 16:00). At this time, the ADSS signing services will be down for approximately 10 minutes.
Legacy QuoVadis PrimoSign signing service maintenance – 60-minute downtime
The Legacy QuoVadis PrimoSign signing service maintenance starts at 17:00 CET (UTC 16:00). At this time, this PrimoSign signing service will be down for approximately 60 minutes.
QuoVadis services maintenance – 10-minute downtime
The QuoVadis maintenance starts at 17:00 CET (UTC 16:00). At this time, some QuoVadis services will be down for approximately 10 minutes.
SealSign Cloud
Cert Lookup
QuoVadis Legacy certificate issuance: S/MIME and PrimoSign
idp.quovadisglobal.com
Affected services:
ADSS signing service
Document Trust Manager in the DigiCert® ONE Switzerland location
TrustLink Enterprise in our Switzerland location
Legacy QuoVadis PrimoSign signing
Legacy QuoVadis Services
What can I do?
Plan accordingly:
Schedule high-priority ADSS and PrimoSign document signings before or after the maintenance window.
Schedule high-priority orders, renewals, and reissues before or after the maintenance window.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts for when maintenance starts and ends.
See the DigiCert Europe 2025 maintenance schedule for maintenance dates and times.
Services will be restored as soon as the maintenance is completed.
Upcoming scheduled Global maintenance
The PrimoSign signing services will be down for approximately 60 minutes during scheduled Global maintenance on January 11, 2025, 22:00 – 24:00 MST (January 12, 05:00 – 07:00 UTC).
How does this affect me?
The maintenance starts at 22:00 MST (05:00 UTC). At this time, the PrimoSign signing services will be down for approximately 60 minutes.
Affected services
Document Trust Manager's PrimoSign signing service in the DigiCert® ONE USA location.
What can I do?
Plan accordingly:
Schedule high-priority PrimoSign signing service document signings before or after the maintenance window.
Schedule high-priority orders, renewals, and reissues before or after the maintenance window.
Expect interruptions if you use the APIs for immediate certificate issuance and automated tasks.
Subscribe to the DigiCert Status page for live maintenance updates, including email alerts for when maintenance starts and ends.
See the DigiCert Global 2025 maintenance schedule for maintenance dates and times.
Services will be restored as soon as the maintenance is completed.
January 10, 2025
DigiCert moving to new dedicated IPv4 addresses for our DigiCert services and removing support for IPv6 addresses
On January 10, 2025, at 08:00 MST (15:00 UTC), DigiCert must assign new dedicated IPv4 addresses to several services. We will also remove support for IPv6 addresses at this time.
Why is DigiCert adding moving to new dedicated IPv4 addresses and removing support for IPv6 addresses?
Our current CDN (content delivery network) is discontinuing its services, forcing us to move to a new service platform before the services end, which is why we are unable to provide you with more time to prepare. When we move to our new CDN, we will focus only on IPv4 addresses and remove support for IPv6 addresses.
For more details about the new dedicated IPv4 addresses, see our knowledge base article, DigiCert Certificate Status IP Addresses.
What do I need to do?
Does your company use allowlists?
If not, no action is required. Your services will continue to work as they did before the move to the new IPv4 addresses.
If yes, you need to update your allowlists to include the new IPv4 addresses before January 10, 2025, to keep your DigiCert services running as they did before the move to the new IPv4 addresses.
Affected platforms:
CertCentral®
CertCentral® Europe
DigiCert® PKI Platform 8
QuoVadis® TrustLink
DigiCert® ONE USA, Netherlands, Switzerland, and Japan instances*
Affected services:
TLS OCSP
TLS CRL
PKI Platform 8 CRLs
PKI Platform 8 Certificate Authority (CA) certificates
PKI client download
Important
*If your Trust Lifecycle, Software Trust, or Document Trust Manager (USA, CH, NL, JP) uses public certificates from CertCentral Global, CertCentral Europe, or PKI Platform 8, you may want to add these IP addresses to your allowlist.
OCSP or CRL distribution endpoints using any of the following subdomains are not affected:
one.digicert.com
one.nl.digicert.com
one.ch.digicert.com
one.digicert.co.jp
one.oracle.digicert.com
January 8, 2025
End of life for HTTPS web-based WHOIS lookups and reuse of domain validations where a WHOIS lookup was used
On January 8, 2025, DigiCert will make the following changes to our domain validation process per new industry requirements:
Stop using manual/HTTPS web-based WHOIS lookups to obtain domain contact information for domain control validation.
No longer reuse existing domain validations where a manual/HTTPS web-based WHOIS lookup was used to collect domain contact information, regardless of whether the previously obtained information is within the allowed 397-day reuse period.
These changes affect all web-based WHOIS domain validations, including the following certificate types: TLS, Verified Mark and Common Mark, Secure Email (S/MIME), DirectAssured, and DirectTrust. See End of life for WHOIS-based DCV methods.
How does this affect me?
Are you using the WHOIS-based Email or Phone DCV methods to validate your domains, and has DigiCert’s automated WHOIS lookup ever failed to retrieve your desired email address for your domains?
If you answered yes to both questions above, then you are probably impacted. Starting January 8, your email or phone domain control validation could fail if it relies on a manual/HTTPS web-based WHOIS lookup by our validation agents.
Important
The manual/HTTPS web-based WHOIS lookup changes do not affect your existing certificates. Your certificates will remain valid and trusted until they expire.
What do I need to do?
Do you rely on immediate certificate issuance?
If not, then no action is required until the next time you order a certificate.
The next time you order a certificate, you must choose a non-WHOIS-reliant domain control validation (DCV) method, such as DNS Text Record. To continue validating domains via email, set up a DNS TXT Email Contact or a Constructed Email address.
If yes, then action is required to avoid potential disruption to your certificate issuance.
For those that rely on instant issuance of certificates, you must revalidate your domains using a non-WHOIS-reliant DCV method , such as DNS Text Record, or to continue validating domains via email, set up a DNS TXT Email Contact or a Constructed Email address before January 8.
Why will DigiCert stop using manual/HTTPS web-based WHOIS lookups and reusing existing domain validations where a manual/HTTPS web-based WHOIS lookup was used?
The industry recently adopted Ballot SC-80v3: Sunset the Use of WHOIS to Identify Domain Contacts and Relying DCV Methods. To comply with industry changes mandated by the ballot, certificate authorities (CAs), such as DigiCert, must stop using WHOIS to identify domain contacts for email, fax, SMS, postal mail, and phone domain control validation (DCV) methods. Note that DigiCert only supports the email and phone WHOIS-based DCV methods.
References